
A brief description of the "Basic Principle" and how it can be used to test for primality.
From playlist Cryptography and Coding Theory

Introduction - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security

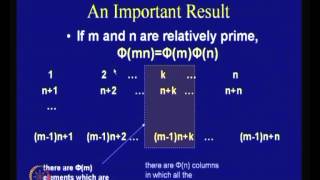
Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
This video gives a general introduction to cryptography WITHOUT actually doing any math. Terms covered include cryptology vs cryptography vs cryptanalysis, symmetric vs public key systems, and "coding theory." NOTE: Yes, I said and wrote "cryptOanalysis" when it's actually "cryptanalysis
From playlist Cryptography and Coding Theory

Challenge Question - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Introduction To CISSP | CISSP Training Videos
Simplilearn’s CISSP certification training is aligned to the (ISC) ² CBK 2015 and trains you in the industry’s latest best practices, which will help you ace the exam in the first attempt. The certification helps you develop the expertise in defining the architecture, in designing, buildin
From playlist CISSP Training Videos [2022 Updated]

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

(IC 1.1) Information theory and Coding - Outline of topics
A playlist of these videos is available at: http://www.youtube.com/playlist?list=PLE125425EC837021F Overview of central topics in Information theory and Coding. Compression (source coding) theory: Source coding theorem, Kraft-McMillan inequality, Rate-distortion theorem Error-correctio
From playlist Information theory and Coding

Where Did Bitcoin Come From? – The True Story
Join my Discord Community today - https://discord.gg/coldfusion - Thanks to Discord for sponsoring today’s video. Episode 2 of the Bitcoin story: https://youtu.be/iYn6EQDqTkU --- About ColdFusion --- ColdFusion is an Australian based online media company independently run by Dagogo Altra
From playlist Blockchain and Crypto

Spotlight: Life without Cryptography
Strip away the trimmings of a traditional science presentation, add cocktails, and you have WSF Spotlight. How much of your information would you rather stay hidden from public view? Using a hypothetical scenario, and with the help of her two daughters, Tal Rabin describes a world without
From playlist SPOTLIGHT: Innovation from Unexpected Places

Hacking at Quantum Speed with Shor's Algorithm | Infinite Series
Viewers like you help make PBS (Thank you 😃) . Support your local PBS Member Station here: https://to.pbs.org/donateinfi Classical computers struggle to crack modern encryption. But quantum computers using Shor’s Algorithm make short work of RSA cryptography. Find out how. Tweet at us! @
From playlist Cryptography 101

Welcome to a series of films where our researchers talk about their latest work in two minutes or less. In the first series you can watch: Ofir Gorodetsky on analytic number theory Cristina Anghel on quantum topology (case study below) https://www.maths.ox.ac.uk/node/39626 Patrick Hough
From playlist Research Stories

In this session, Cory discusses the tools for using cryptography in Swift, and introduces a new Apple open source project for working with cryptography on all platforms, Swift Crypto. PUBLICATION PERMISSIONS: Original video was published with the Creative Commons Attribution license (reus
From playlist Blockchain

How to Convert a Negative Integer in Modular Arithmetic - Cryptography - Lesson 4
In this video, I explain how to convert a negative integer to a congruent integer within a given modulo. Join this channel to get access to perks: https://www.youtube.com/channel/UCn2SbZWi4yTkmPUj5wnbfoA/join :)
From playlist Cryptography
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

How to Break Cryptography | Infinite Series
Viewers like you help make PBS (Thank you 😃) . Support your local PBS Member Station here: https://to.pbs.org/donateinfi Only 4 steps stand between you and the secrets hidden behind RSA cryptography. Find out how to crack the world’s most commonly used form of encryption. Tweet at us! @p
From playlist Cryptography 101