Cryptographic primitives | Cryptography | Hashing | Cryptographic hash functions
Cryptographic hash function
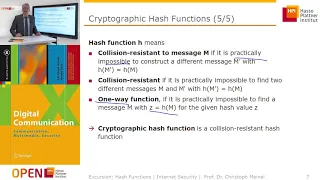
A cryptographic hash function (CHF) is a mathematical algorithm that maps data of an arbitrary size (often called the "message") to a bit array of a fixed size (the "hash value", "hash", or "message digest"). It is a one-way function, that is, a function for which it is practically infeasible to invert or reverse the computation. Ideally, the only way to find a message that produces a given hash is to attempt a brute-force search of possible inputs to see if they produce a match, or use a rainbow table of matched hashes. Cryptographic hash functions are a basic tool of modern cryptography. A cryptographic hash function must be deterministic, meaning that the same message always results in the same hash. Ideally it should also have the following properties: * it is quick to compute the hash value for any given message * it is infeasible to generate a message that yields a given hash value (i.e. to reverse the process that generated the given hash value) * it is infeasible to find two different messages with the same hash value * a small change to a message should change the hash value so extensively that a new hash value appears uncorrelated with the old hash value (avalanche effect) Cryptographic hash functions have many information-security applications, notably in digital signatures, message authentication codes (MACs), and other forms of authentication. They can also be used as ordinary hash functions, to index data in hash tables, for fingerprinting, to detect duplicate data or uniquely identify files, and as checksums to detect accidental data corruption. Indeed, in information-security contexts, cryptographic hash values are sometimes called (digital) fingerprints, checksums, or just hash values, even though all these terms stand for more general functions with rather different properties and purposes. (Wikipedia).