Watch more videos on http://www.brightstorm.com/science/chemistry SUBSCRIBE FOR All OUR VIDEOS! https://www.youtube.com/subscription_center?add_user=brightstorm2 VISIT BRIGHTSTORM.com FOR TONS OF VIDEO TUTORIALS AND OTHER FEATURES! http://www.brightstorm.com/ LET'S CONNECT! Facebook ► h
From playlist Chemistry

What happens when two objects collide? License: Creative Commons BY-NC-SA More information at http://k12videos.mit.edu/terms-conditions
From playlist Physics

Elastic and Inelastic Collisions
When you take a shot on a pool table or tackle someone in a football game, you're participating in a collision. But the two events we just mentioned are totally different kinds of collisions! But what are elastic collisions, and what are inelastic collisions? We have to learn the varieties
From playlist Classical Physics

Tutorial: GeoHTTP Remote Buffer Overflow and DoS
A real example of a Buffer Overflow/Denial of Service attack! My favorite video: http://www.youtube.com/watch?v=z00kuZIVXlU Visit http://binslashshell.wordpress.com and join our forum community!!! This is a video showing what a Buffer Overflow Aattck can do to a Web Server. For th
From playlist Denial of Service attacks

Coding Math: Episode 14 - Collision Detection
This week we look at the basics of collision detection and a few of the simplest, most common methods for achieving it. Support Coding Math: http://patreon.com/codingmath Source Code: http://github.com/bit101/codingmath
From playlist Episodes

Watch more videos on http://www.brightstorm.com/science/chemistry SUBSCRIBE FOR All OUR VIDEOS! https://www.youtube.com/subscription_center?add_user=brightstorm2 VISIT BRIGHTSTORM.com FOR TONS OF VIDEO TUTORIALS AND OTHER FEATURES! http://www.brightstorm.com/ LET'S CONNECT! Facebook ► h
From playlist Chemistry

The Weaponization of Outbreaks: Crash Course Outbreak Science #5
A sad reality that we have to face when studying outbreak science is that sometimes groups of people use outbreaks intentionally to inflict harm on another group. We call this "weaponizing an outbreak", and it's the focus of this episode of Crash Course Outbreak Science. In this episode we
From playlist Outbreak Science

Collisions: Crash Course Physics #10
Get Your Crash Course Physics Mug here: http://store.dftba.com/products/crashcourse-physics-mug COLLISIONS! A big part of physics is understanding collisions and how they're not all the same. Mass, momentum, and many other things dictate how collisions can be unique. In this episode of Cr
From playlist Physics

NOTACON 2: Recent Attacks Against Hash Functions
Speaker: Matthew Fanto In recent months, a large amount of research into the security of cryptographic hash functions has revealed serious flaws in every widely used hash function, including MD4, MD5, RIPEMD, HAVAL, SHA-0, and SHA-1. These flaws have far reaching consequences, as hash fun
From playlist Notacon 2

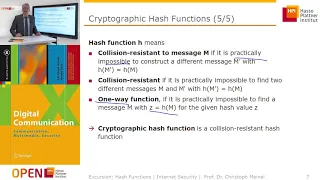
Cryptographic Hash Functions (Contd...2)
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
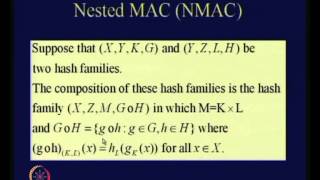
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

From playlist Cryptography Lectures

25c3: Making the theoretical possible
From playlist 25C3: Nothing to hide

DDoS Attack Explained | What Is DDoS Attack? | Cyber Security Training | Simplilearn
This video on "What is a DDoS attack?" will help you understand all about a DDoS attack. Distributed Denial of Service (DDoS) attack is one of the most dangerous forms of cyberattacks. In this video, we will start with a few real-life scenarios of DDoS attacks and then learn about a DDoS a
From playlist Ethical Hacking Playlist [2023 Updated] 🔥

How To Create A Multiplayer Fighting Game In Unreal Engine | Session 09 | #gamedev
Don’t forget to subscribe! This project series is about how to create a multiplayer fighting game in Unreal Engine. In this series, we will go over the requirements of setting up a multiplayer fighting game with two human players (no AI). The goal is to deplete your opponent's health t
From playlist Create A Multiplayer Fighting Game In Unreal Engine

CERIAS Security: Recent Attacks on MD5 2/6
Clip 2/6 Speaker: John Black · University of Colorado at Boulder Cryptology is typically defined as cryptography (the construction of cryptographic algorithms) and cryptanalysis (attacks on these algorithms). Both are important, but the latter is more fun. Cryptographic hash functions
From playlist The CERIAS Security Seminars 2006

CERIAS Security: Recent Attacks on MD5 5/6
Clip 5/6 Speaker: John Black · University of Colorado at Boulder Cryptology is typically defined as cryptography (the construction of cryptographic algorithms) and cryptanalysis (attacks on these algorithms). Both are important, but the latter is more fun. Cryptographic hash functions
From playlist The CERIAS Security Seminars 2006

Strong Collision Resistance - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

SYN Flood Denial of Service attack using perl script and hping3 tool.
From playlist Denial of Service attacks