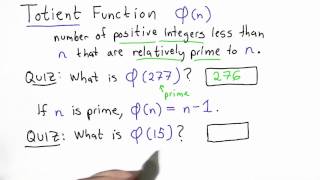
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Correctness And Security - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cipher Block Chaining Mode - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Importance Of Keys Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Trusted Third Party Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Voter Identity Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Private Messages Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Protection Of Information Assets | CISA Training Videos
Certified Information System Auditor (CISA) Protection of Information Assets Objectives: • Understand and provide assurance that the enterprise’s security policies, standards, procedures and controls ensure the confidentiality, integrity and availability of information assets • Detail the
From playlist CISA Training Videos

RailsConf 2022 - Service Denied! Understanding How Regex DoS Attacks Work by Kevin Menard
Did you know that people can knock your Rails application offline just by submitting specially formatted strings in a form or API request? In this talk, we’ll take a look at what’s really going on with a regex denial of service (DoS) attack. We’ll take a peek into the CRuby regex engine to
From playlist RailsConf 2022

Ethical Hacking Full Course | Ethical Hacker Course For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseNov16-VL5261WGa70&utm_medium=DescriptionFF&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_ca
From playlist Simplilearn Live

Certified Ethical Hacker V10 Tutorial | CEH V10 Tutorial | CEH V10 Training Video | CEH |Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=EthicalHackerV10Tutorial-xbZErsH_-CI&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cyb
From playlist Ethical Hacking Playlist [2023 Updated] 🔥

Nexus Trimester - Delaram Kahrobaei (City University of New York)
Cryptosystems Based on Group-Theoretic Problems: A Survey, New Results, Open Problems Delaram Kahrobaei (City University of New York) March 31, 2016 Abstract: In this talk I will survey some of the cryptosystems based on group theoretic problems and their computational complexity such as
From playlist Nexus Trimester - 2016 - Secrecy and Privacy Theme

Ethical Hacking Full Course 2022 | Ethical Hacking Course For Beginners 2022 | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseJan7&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_campaig
From playlist Simplilearn Live

Mathematics in Cryptography III - Toni Bluher
2018 Program for Women and Mathematics Topic: Mathematics in Cryptography III Speaker: Toni Bluher Affiliation: National Security Agency Date: May 24, 2018 For more videos, please visit http://video.ias.edu
From playlist Mathematics

Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

Anne Broadbent - Information-Theoretic Quantum Cryptography Part 1 of 2 - IPAM at UCLA
Recorded 27 July 2022. Anne Broadbent of the University of Ottawa presents "Information-Theoretic Quantum Cryptography" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: These lectures are an introduction to the interplay between quantum information and cryp
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Challenge Question - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

CERIAS Security: Watermarking Relational Databases 2/6
Clip 2/6 Speaker: Mohamed Shehab · Purdue University Proving ownership rights on outsourced relational databases is a crucial issue in today internet-based application environment and in many content distribution applications. In this talk, we will present mechanisms for proof of owne
From playlist The CERIAS Security Seminars 2005 (2)