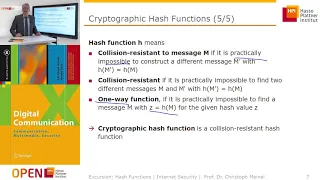
Cryptographic Hash Functions: Part 1
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security
Cryptographic Hash Functions: Part 2
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

From playlist Cryptography Lectures

Cryptographic Hash Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
From playlist Cryptography Lectures

Bitcoin - Cryptographic hash function
Courses on Khan Academy are always 100% free. Start practicing—and saving your progress—now: https://www.khanacademy.org/economics-finance-domain/core-finance/money-and-banking/bitcoin/v/bitcoin-cryptographic-hash-function What cryptographic hash functions are and what properties are des
From playlist Money, banking and central banks | Finance and Capital Markets | Khan Academy

Overview on Modern Cryptography
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

NOTACON 2: Recent Attacks Against Hash Functions
Speaker: Matthew Fanto In recent months, a large amount of research into the security of cryptographic hash functions has revealed serious flaws in every widely used hash function, including MD4, MD5, RIPEMD, HAVAL, SHA-0, and SHA-1. These flaws have far reaching consequences, as hash fun
From playlist Notacon 2

DjangoCon 2014- Practical Django Secuirty
By, Levi Gross Web application security is an ever present problem. The "don't trust user input" mantra sounds nice but doesn't practically work. In this talk we will go over introduce and apply a set of practical programming paradigms that you can use to write secure code. Help us captio
From playlist DjangoCon 2014

CERIAS Security: Recent Attacks on MD5 1/6
Clip 1/6 Speaker: John Black · University of Colorado at Boulder Cryptology is typically defined as cryptography (the construction of cryptographic algorithms) and cryptanalysis (attacks on these algorithms). Both are important, but the latter is more fun. Cryptographic hash functions
From playlist The CERIAS Security Seminars 2006

Cryptography Tutorial For Beginners | Cybersecurity Training | Edureka | Cybersecurity Live - 2
🔥Edureka Cyber Security Course: https://www.edureka.co/cybersecurity-certification-training This Edureka video on "Cryptography Tutorial" gives an introduction to the Cryptography and talks about its basic concepts. 🔴Subscribe to our channel to get video updates. Hit the subscribe butto
From playlist Edureka Live Classes 2020

OWASP AppSecUSA 2011:How NOT to Implement Cryptography for the OWASP Top 10 (Reloaded)
Speaker: Anthony J. Stieber This talk is an update of a talk in 2008 at the OWASP Minneapolis-St.Paul Chapter which was about encryption as it applies to parts of the OWASP Top Ten. The new talk uses fresh examples of application cryptography successes and failures, and also incorporates
From playlist OWASP AppSecUSA 2011

3. Blockchain Basics & Cryptography
MIT 15.S12 Blockchain and Money, Fall 2018 Instructor: Prof. Gary Gensler View the complete course: https://ocw.mit.edu/15-S12F18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP63UUkfL0onkxF6MYgVa04Fn In this lecture, Prof. Gensler, explains the basics of blockchain an
From playlist MIT 15.S12 Blockchain and Money, Fall 2018

Correctness And Security - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography