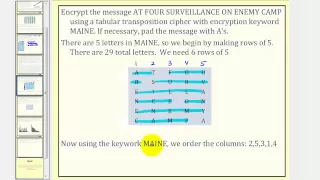
Cryptography: Transposition Cipher
This lesson explains how to encrypt and decrypt a message using a transposition cipher. Site: http://mathispower4u.com
From playlist Cryptography
In this very easy and short tutorial I explain the concept of the transpose of matrices, where we exchange rows for columns. The matrices have some properties that you should be aware of. These include how to the the transpose of the product of matrices and in the transpose of the invers
From playlist Introducing linear algebra
What is the transpose of a matrix?
What is the transpose of a matrix? Here it is defined and some simple examples are discussed. Free ebook http://tinyurl.com/EngMathYT
From playlist Intro to Matrices

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

This video defines the transpose of a matrix and explains how to transpose a matrix. The properties of transposed matrices are also discussed. Site: mathispower4u.com Blog: mathispower4u.wordpress.com
From playlist Introduction to Matrices and Matrix Operations

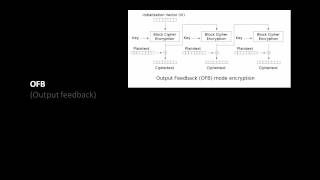
Pseudorandom Number Generation and Stream Ciphers
Fundamental concepts of Pseudorandom Number Generation are discussed. Pseudorandom Number Generation using a Block Cipher is explained. Stream Cipher & RC4 are presented.
From playlist Network Security

Linear Algebra 11w: Introduction to the Transpose of a Matrix
https://bit.ly/PavelPatreon https://lem.ma/LA - Linear Algebra on Lemma http://bit.ly/ITCYTNew - Dr. Grinfeld's Tensor Calculus textbook https://lem.ma/prep - Complete SAT Math Prep
From playlist Part 1 Linear Algebra: An In-Depth Introduction with a Focus on Applications

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

How Encryption Keeps Your Data Safe
Start protecting yourself on the web at https://NordVPN.com/SCISHOW or use code SCISHOW to save 75% off of a 3-year Virtual Private Network plan, plus 1 month free. Keeping our data safe and secure is necessary in today's world, but a lot of the encryption we depend on has been in devel
From playlist Uploads
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography
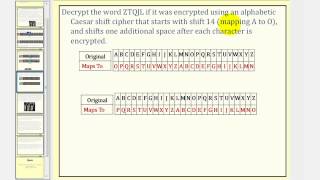
Cryptography: Caesar Cipher With Shift
This lesson explains how to encrypt and decrypt a message using Caeser cipher with a shift. Site: http://mathispower4u.com
From playlist Cryptography

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
DEFCON 18: Tales from the Crypt 1/4
Speaker: G. Mark Hardy Learn how to crack crypto contests like a pro. The speaker has awarded half a dozen free round-trip plane tickets to previous contest winners. Maybe you'll be next. From the daily newspaper puzzle to badge contests to codes that keep the National Security Agency a
From playlist DEFCON 18-1
What is Cryptography? | Introduction to Cryptography | Cryptography for Beginners | Edureka
🔵Edureka Cyber Security Masters Program: https://bit.ly/3pfHHIN 🔥Edureka CompTIA Security+ Certification Training: https://bit.ly/3nxeVRl Cryptography is essential to protect the information shared across the internet. This video on What is cryptography explaines you the fundamental concep
From playlist Cyber Security Training for Beginners | Edureka

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Toy Substitution Cipher 2 Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography