
Intro to HTML and CSS. Part of a larger series. Visit codeschool.org
From playlist HTML and CSS

In this video, you’ll learn about HTML and how it is used to code webpages. We hope you enjoy! To learn more, check out our Basic HTML tutorial here: https://edu.gcfglobal.org/en/basic-html/ #whatishtml #htmlcode #learnhtml
From playlist HTML

In this video, you’ll learn more about how hashtags are used on Twitter. Visit https://www.gcflearnfree.org/twitter/what-is-a-hashtag/1/ for our text-based lesson. This video includes information on: • Using hashtags • Browsing popular hashtags We hope you enjoy!
From playlist Twitter

From playlist CS50 Shorts 2013

Preparing Your Resume for the Internet
In this video, you’ll learn more about making your resume Internet-ready. Visit https://www.gcflearnfree.org/resumewriting/preparing-your-resume-for-the-internet/1/ for our text-based lesson. This video includes information on: • Emailing your resume • Creating and formatting a plain-text
From playlist Job Applications

Posting Articles, Images, Video, etc. in Wordpress
I go into detail on what types of posts attract people. Then I de-jargonize the whole process of creating, editing, and search engine optimizing posts. From Design To Web Setting Up Blog
From playlist Wordpress Tutorial

In this video, you’ll learn more about using Messages in LinkedIn. Visit https://edu.gcfglobal.org/en/linkedin/keeping-up-with-linkedin/1/ for our text-based lesson. We hope you enjoy!
From playlist LinkedIn

If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Communicating Effectively

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
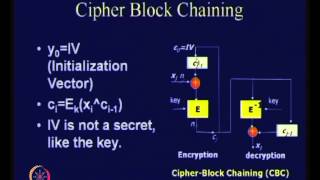
Modes of Operation of Block Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
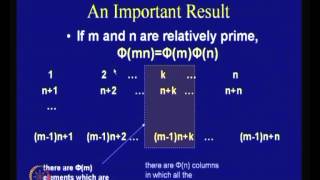
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

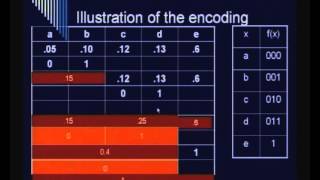
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

What is Cryptography - Introduction to Cryptography - Lesson 1
In this video I explain the fundamental concepts of cryptography. Encryption, decryption, plaintext, cipher text, and keys. Join this channel to get access to perks: https://www.youtube.com/channel/UCn2SbZWi4yTkmPUj5wnbfoA/join :)
From playlist Cryptography

If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Graphic Design

Affine Cipher - Decryption (Known Plaintext Attack)
In this video I talk about ways to decrypt the Affine Cipher when the key is NOT known. Specifically, I go over an example of the known plaintext attack. 3^(-1) = 9 (mod 26) math worked out (Euclidean Algorithm): 1. Forwards: 26 = 3(8) + 2 3 = 2(1) + 1 2. Backwords: 1 = 3 -
From playlist Cryptography and Coding Theory

Types of Cryptography Algorithms | Cryptography in Network Security | Edureka | Cybersecurity Live-2
🔥Edureka Cybersecurity Online Training: https://www.edureka.co/cybersecurity-certification-training This Edureka video on Cryptography Algorithms Explained talks about the various algorithms used for cryptography and how they help in making our data secure. Cybersecurity Training Playlist
From playlist Edureka Live Classes 2020

Anchor text is the text associated with a hyperlink. A search engine treats it as a condensed summary of a webpage at the end of the hyperlink. Anchor text is indexed in addition to the content of the page itself, and used for matching the queries.
From playlist IR15 Web Search and PageRank
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
