
How Encryption Keeps Your Data Safe
Start protecting yourself on the web at https://NordVPN.com/SCISHOW or use code SCISHOW to save 75% off of a 3-year Virtual Private Network plan, plus 1 month free. Keeping our data safe and secure is necessary in today's world, but a lot of the encryption we depend on has been in devel
From playlist Uploads

ADFGVX Cipher: Encryption and Decryption (Updated)
Encryption and Decryption of the World War One ADFGVX Cipher, through examples. This video replaces an earlier one with the same content, but has some improvements and corrections. #cryptography
From playlist Classical Cryptography

ADFGVX Cipher: Encryption and Decryption (OLD VERSION: SEE NEW VERSION LINK BELOW)
This video has been replaced with an updated video: visit https://youtu.be/T0xfKiU9Rr4 Encryption and Decryption of the World War One ADFGVX Cipher, through examples.
From playlist Classical Cryptography
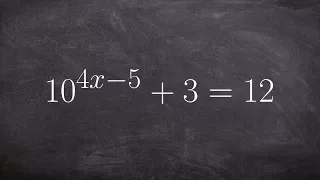
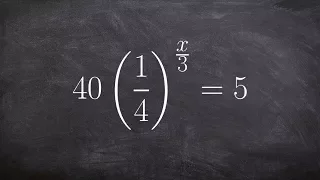
Use inverse operation to solve exponential equation without one to one property
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms

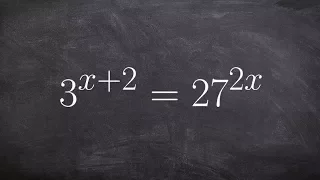
Learn basics for solving an exponential equation by using one to one property
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms

Solving an exponential equation using the one to one property 16^x + 2 = 6
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms
Using the equality of exponents to get the same base and solve
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations without a Calculator

Using the inverse of an exponential equation to find the logarithm
👉 Learn how to convert an exponential equation to a logarithmic equation. This is very important to learn because it not only helps us explain the definition of a logarithm but how it is related to the exponential function. Knowing how to convert between the different forms will help us i
From playlist Logarithmic and Exponential Form | Learn About
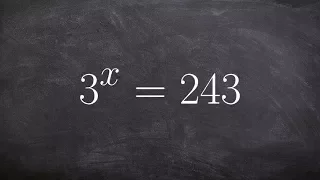
Using one to one properties to solve an exponential equation
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations without a Calculator
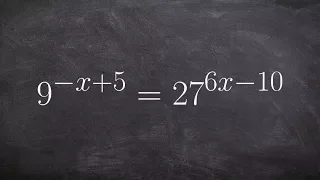
Using one to one property with different bases to solve an exponential equation
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations without a Calculator
Solve an exponential equation using one to one property and isolating the exponent
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms

How to solve an exponential equation with two different bases
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations without a Calculator

Follow-up: Barbie electronic typewriter
Here is a copy of the description from the Barbie video: ---- I first found this story on the crypto museum website, which has great information about the Barbie typewriter (and other cipher machines) https://www.cryptomuseum.com/crypto/mehano/barbie/ ------- Thanks to Sarah Everett fr
From playlist My Maths Videos

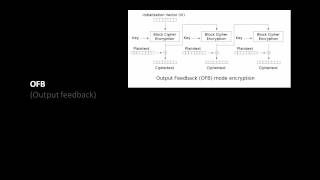
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Live CEOing Ep 544: Language Design in Wolfram Language [Ciphers & WFR Submissions] [Part 01]
In this episode of Live CEOing, Stephen Wolfram discusses upcoming improvements and features to the Wolfram Language. If you'd like to contribute to the discussion in future episodes, you can participate through this YouTube channel or through the official Twitch channel of Stephen Wolfram
From playlist Behind the Scenes in Real-Life Software Design
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

What is Bill Cipher? (Scientific Analysis)
What is Bill Cipher? Today we discover the very very confusing science of what Gravity Fall's Bill Cipher is. =======WARNING VERY VERY CONFUSING======= This video talks about dimensions and alternate universes. Your mind might explode! Sources: -http://en.wikipedia.org/wiki/Four-dim...
From playlist Scientific Videos

Solving exponential equation the easy way one to one properties
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations without a Calculator

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security