
Thwarting Dictionary Attacks - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Thwarting Dictionary Attacks Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Editing Wikipedia has never been easier using the new Visual Editor interface which makes editing Wikipedia as easy as using Microsoft Word or Wordpress blogs. This 1 hour workshop is aimed primarily at anyone who is interested in learning how to edit Wikipedia but, up until now, were ne
From playlist How to edit Wikipedia - September 2020 playlist

Clojure - the Reader and Evaluator (4/4)
Part of a series teaching the Clojure language. For other programming topics, visit http://codeschool.org
From playlist the Clojure language
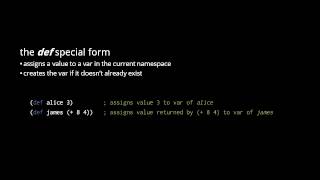
Clojure - the Reader and Evaluator (2/4)
Part of a series teaching the Clojure language. For other programming topics, visit http://codeschool.org
From playlist the Clojure language

SYN Flood Denial of Service attack using perl script and hping3 tool.
From playlist Denial of Service attacks

Tutorial: GeoHTTP Remote Buffer Overflow and DoS
A real example of a Buffer Overflow/Denial of Service attack! My favorite video: http://www.youtube.com/watch?v=z00kuZIVXlU Visit http://binslashshell.wordpress.com and join our forum community!!! This is a video showing what a Buffer Overflow Aattck can do to a Web Server. For th
From playlist Denial of Service attacks

Is A DOS Attack A Weapon? | Idea Channel | PBS Digital Studios
Viewers like you help make PBS (Thank you 😃) . Support your local PBS Member Station here: https://to.pbs.org/donateidea Here's an idea: a DOS attack is a weapon. Denial of Service (DOS) or Distributed Denial of Service (DDOS) attacks take down servers by distracting them with meaningles
From playlist Newest Episodes

This is a single lecture from a course. If you you like the material and want more context (e.g., the lectures that came before), check out the whole course: http://users.umiacs.umd.edu/~jbg/teaching/CMSC_470/ (Including homeworks and reading.) Music: https://soundcloud.com/alvin-grisso
From playlist Computational Linguistics I

DEFCON 16: Buying Time - What is your Data Worth?
Speaker: Adam Bregenzer, Security Researcher Brute Force attacks are often marginalized as a user issue or discounted as a non-issue because of sufficient password complexity. Because rainbow tables have provided a re-invigoration of this type of attack, maintaining password security is s
From playlist DEFCON 16

Black Hat USA 2010: Understanding the Windows SMB NTLM Weak Nonce Vulnerability 2/5
Speakers: Hernan Ochoa, Agustin Azubel In February 2010, we found a vulnerability in the SMB NTLM Windows Authentication mechanism that have been present in Windows systems for at least 14 years (from Windows NT 4 to Windows Server 2008). You probably haven't heard about this vulnerabilit
From playlist BH USA 2010 - OS WARS

Password Exploitation Class: Part 2: Hashcat and OCLHashcat 5/6
Clip 5/6 Credits: irongeek.com This is a class we gave for the Kentuckiana ISSA on the the subject of password exploitation. The Password Exploitation Class was put on as a charity event for the Matthew Shoemaker Memorial Fund ( http://www.shoecon.org/ ). The speakers were Dakykilla,
From playlist Password Exploitation Class

Ethical Hacking - Basics Of Ethical Hacking | Session 04 | #crybersecurity
Don’t forget to subscribe! This project will cover the basics to start ethical hacking and learn the tools and techniques of the industry. This project should teach someone how with limited or no hacking experience and teach them the basics to get started in the cyber security industry.
From playlist Basics Of Ethical Hacking

Black Hat USA 2010: Understanding the Windows SMB NTLM Weak Nonce Vulnerability 4/5
Speakers: Hernan Ochoa, Agustin Azubel In February 2010, we found a vulnerability in the SMB NTLM Windows Authentication mechanism that have been present in Windows systems for at least 14 years (from Windows NT 4 to Windows Server 2008). You probably haven't heard about this vulnerabilit
From playlist BH USA 2010 - OS WARS

This Is How Hackers Crack Your Password | Password Cracking and Brute Force Tools | Simplilearn
In this video on how hackers crack your password, we are going to cover the basics of password cracking and brute force tools. Multiple techniques of cracking passwords are also covered, along with the variety of tools being used by malicious hackers worldwide to steal user credentials. La
From playlist Cyber Security Playlist [2023 Updated]🔥

Password Cracking - Computerphile
'Beast' cracks billions of passwords a second, Dr Mike Pound demonstrates why you should probably change your passwords... Please note,at one point during the video Mike suggests using SHA512. Please check whatever the recommended process is at the time you view the video. Here's a look
From playlist Cryptography on Numberphile and Computerphile

How To Crack WiFi (Wireless) Networks Using Cow Patty and Air-Crack | Introduction | #cybersecurity
Don’t forget to subscribe! In this tutorial series, you will learn to crack WiFi ( Wireless ) networks. We will use Cow Patty and Air-Crack in this tutorial to crack the WiFi networks. In this project, you will learn how to crack different Wireless networks including WEP, WPA, WPA2 netw
From playlist Crack WiFi (Wireless) Networks Using Cow Patty and Air-Crack

Computer Security | What Is Computer Security | Cyber Security Tutorial | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=ComputerSecurity-cs3B0zcRJco&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecuri
From playlist Cyber Security Playlist [2023 Updated]🔥

