On Zaremba's Conjecture - Alex Kontorovich
Alex Kontorovich Stony Brook University April 22, 2011 Inspired by the theory of good lattice points in numerical integration, Zaremba conjectured in 1972 that for every denominator q, there is some coprime numerator p, such that the continued fraction expansion of p/q has uniformly bounde
From playlist Mathematics

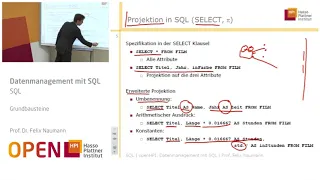
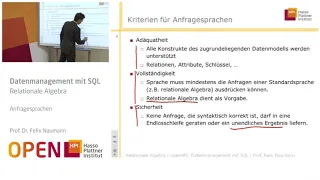
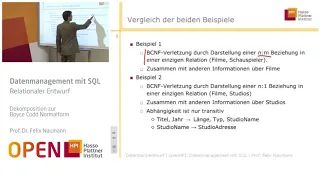
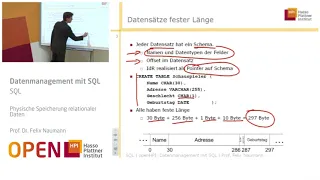
From playlist Datenmanagement mit SQL bei Dr. Felix Naumann

Asymmetric Cryptosystems - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

From playlist Datenmanagement mit SQL bei Dr. Felix Naumann

One Way Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

26C3: Yes We Cant - on kleptography and cryptovirology 5/6
Clip 5/6 Speaker: Moti Yung In this talk I will survey some of the results (with Adam Young) on Cryptovirology (the art of employing public key cryptography maliciously as part of a malware attack, such as in ransomware) and the related Kleptography (the art of embedding cryptographic
From playlist 26C3: Here be dragons day 3
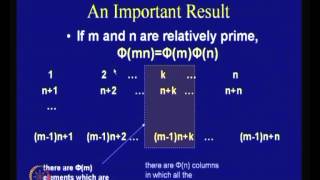
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptography - Seminar 1 - Foundations
This seminar series is about the mathematical foundations of cryptography. In the first seminar Eleanor McMurtry introduces cryptography and explains some of the problems that need to be solved in order to develop proper foundations. The webpage for this seminar is https://lnor.net/uc-sem
From playlist Metauni

Stanford Seminar - The Evolution of Public Key Cryptography
EE380: Computer Systems Colloquium Seminar The Evolution of Public Key Cryptography Speaker: Martin Hellman, Stanford EE (Emeritus) While public key cryptography is seen as revolutionary, after this talk you might wonder why it took Whit Diffie, Ralph Merkle and Hellman so long to discov
From playlist Stanford EE380-Colloquium on Computer Systems - Seminar Series

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

CERIAS Security: Perturbation of Multivariable Public-key Cryptosystems 1/5
Clip 1/5 Speaker: Jintai Ding · University of Cincinnati Public key cryptography is an indispensable part of most modern communication systems. However, quantum computers can break cryptosystems like RSA, which are based on For more information go to the Cerias website (http://bit
From playlist The CERIAS Security Seminars 2005 (2)