
Alain Couvreur - Comment domestiquer les codes de Goppa sauvages?
Le schéma de McEliece est un schéma de chiffrement basé sur les codes correcteurs d'erreurs dont la sécurité repose sur la difficulté à décoder un code aléatoire. Parmi les différentes familles de codes algébriques proposées pour ce schéma, les codes de Goppa classiques sont les seuls à ré
From playlist Journées Codage et Cryptographie 2014

Seminar on Applied Geometry and Algebra (SIAM SAGA): Gretchen Matthews
Title: Multivariate Goppa Codes Speaker: Gretchen Matthews, Virginia Tech Date: Tuesday, May 10, 2022 at 11:00am Eastern Abstract: Goppa codes were introduced in 1971 by V. D. Goppa using a univariate polynomial g(x), called a generator polynomial, over a finite field. Properties of the G
From playlist Seminar on Applied Geometry and Algebra (SIAM SAGA)

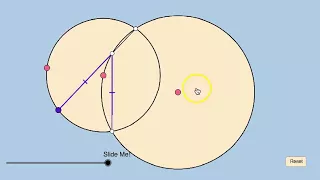
Link: https://www.geogebra.org/m/kSYmnker
From playlist Geometry: Challenge Problems

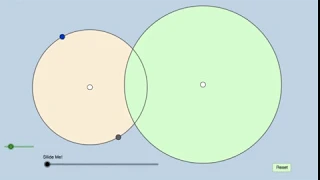
Link: https://www.geogebra.org/m/nH2cAsTz
From playlist Geometry: Challenge Problems

Link: https://www.geogebra.org/m/dMNUJHTa
From playlist Geometry: Challenge Problems
Link: https://www.geogebra.org/m/EtHMAgRw
From playlist Geometry: Challenge Problems

Link: https://www.geogebra.org/m/S4uhMj8J
From playlist Geometry: Challenge Problems

Link: https://www.geogebra.org/m/KUABuvZ2
From playlist Geometry: Challenge Problems

Link: https://www.geogebra.org/m/FzHhdUBn
From playlist Geometry: Challenge Problems

Link: https://www.geogebra.org/m/nXvKNUHa
From playlist Geometry: Challenge Problems

Mirror symmetry for complex projective space and optimal towers of algebraic curves by Sergey Galkin
Date/Time: Monday, March 2, 4:00 pm Title: Mirror symmetry for complex projective space and optimal towers of algebraic curves Abstract: I will speak about mirror symmetry for projective threespace, and how with Sergey Rybakov we used it to construct an optimal tower of algebraic curves
From playlist Seminar Series

How To Convert Gray Code to Binary and Binary to Gray Code
This video explains how to convert gray code to binary and binary to gray code. My Website: https://www.video-tutor.net Patreon Donations: https://www.patreon.com/MathScienceTutor Amazon Store: https://www.amazon.com/shop/theorganicchemistrytutor Subscribe: https://www.youtube.com/cha
From playlist Number Systems

Improving Intermediate Codes - Computerphile
Taking T-Diagrams to the next level, Professor Brailsford tries to improve last episode's intermediate codes. Grateful thanks to Dr Ron Knott for permission to use his set of notes on the porting of compilers, explained using T-diagrams. https://www.facebook.com/computerphile https://t
From playlist Compilers with Professor Brailsford

Binary Trees In Data Structures | Binary Trees & Its Types | Data Structures Tutorial | Simplilearn
🔥Post Graduate Program In Full Stack Web Development: https://www.simplilearn.com/pgp-full-stack-web-development-certification-training-course?utm_campaign=BinaryTreesinDataStructures-JyQgkeqKZyY&utm_medium=DescriptionFF&utm_source=youtube 🔥Caltech Coding Bootcamp (US Only): https://www.si
From playlist Data Structures & Algorithms [2022 Updated]

Bootstrapping with T-Diagrams - Computerphile
How do you compile a compiler? Professor Brailsford starts to unpick the idea of bootstrapping. Bootstrapping: https://youtu.be/nslY1s0U9_c Factory of Ideas - Bell Labs: https://youtu.be/QFK6RG47bww https://www.facebook.com/computerphile https://twitter.com/computer_phile This video
From playlist Compilers with Professor Brailsford

Why Is The PE Entry Point Not The Same As Main SEH and The _security_init_cookie [Patreon Unlocked]
In this tutorial we examine why the entry point for MSVC console applications is not the same as main. We also dive into understanding the __security_init_cookie and __scrt_common_main_seh functions. Expand for more... In this tutorial is part of our RE101 series on Patreon where we disc
From playlist Patreon Unlocked

DEFCON 16: Advanced Software Armoring and Polymorphic Kung Fu
Speaker: Nick Harbour, Principal Consultant, Mandiant This presentation discusses the techniques employed by a new anti-reverse engineering tool named PE-Scrambler. Unlike a traditional executable packer which simply compresses or encrypts the original executable, this tool has the abilit
From playlist DEFCON 16

Link: https://www.geogebra.org/m/W6DkjUwa
From playlist Geometry: Challenge Problems
Link: https://www.geogebra.org/m/ET2ZkXcD
From playlist Geometry: Challenge Problems

Clip 2/6 Speaker: Mathias Payer Hacking the Hackers with User-Space Virtualization In the age of coordinated malware distribution and zero-day exploits security becomes ever more important. This paper presents secuBT, a safe execution framework for the execution of untrusted binary c
From playlist 26C3: Here be dragons day 4