Mathematical problems | Cryptography | Zero-knowledge protocols
Dining cryptographers problem
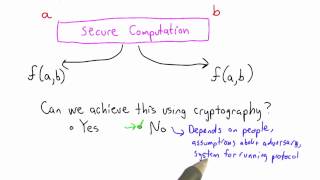
In cryptography, the dining cryptographers problem studies how to perform a secure multi-party computation of the boolean-XOR function. David Chaum first proposed this problem in the early 1980s and used it as an illustrative example to show that it was possible to send anonymous messages with unconditional sender and recipient untraceability. Anonymous communication networks based on this problem are often referred to as DC-nets (where DC stands for "dining cryptographers"). Despite the word dining, the dining cryptographers problem is unrelated to the dining philosophers problem. (Wikipedia).