SSH Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

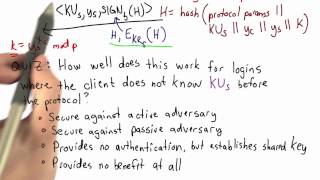
EKE Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Signature Validation - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
OpenSSH Internals for PowerShell Pros by Anthony Nocentino In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd config
From playlist PowerShell + DevOps Global Summit 2018

Correctness And Security - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd configuration, and troubleshooting methods when things go wrong!
From playlist PowerShell + DevOps Global Summit 2018

Free CISSP Training Video | CISSP Tutorial Online Part 2
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CCSPTrainingVideo-XghDe7VlVxo&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecur
From playlist CISSP Training Videos [2022 Updated]

DjangoCon 2019 - Understanding Django authentication by Renato Oliveira
DjangoCon 2019 - Understanding Django authentication by Renato Oliveira Django gives us a built-in authentication system. It's an awesome asset for doing web development strictly with Django, but when you try to do something else, you’ll need to integrate with other options. Understanding
From playlist DjangoCon US 2019

Live CEOing Ep 255: Security-Related Functions in Wolfram Language
Watch Stephen Wolfram and teams of developers in a live, working, language design meeting. This episode is about Security-Related Functions in the Wolfram Language.
From playlist Behind the Scenes in Real-Life Software Design

Lec 22 | MIT 6.033 Computer System Engineering, Spring 2005
Authentication View the complete course at: http://ocw.mit.edu/6-033S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.033 Computer System Engineering, Spring 2005

PowerShell remoting - Installing and troubleshooting in a... by Anthony Nocentino & Richard Siddaway
PowerShell remoting - Installing and troubleshooting in a multiplatform environment PowerShell Core is about choice and the transport layer for remoting is one of those choices. In this session we’ll look at remoting in Multiplatform environments, configuring both OpenSSH and WinRM based
From playlist PowerShell + DevOps Global Summit 2018

Distributed systems, Microservices and Web APIs taking us to new challenges regarding authentication and authorization. - "One does not simply log in!" The standards OAuth2, OpenID Connect, and JSON Web Tokens (JWT) can help us mastering the auth* challenges in these architectures. We'll d
From playlist Talks

OWASP AppSec EU 2013: Improving the Security of Session Management in Web Applications
For more information and to download the video visit: http://bit.ly/appseceu13 Playlist OWASP AppSec EU 2013: http://bit.ly/plappseceu13 Speakers: Lieven Desmet | Wouter Joosen | Frank Piessens | Philippe De Ryck Session management is a critical component of modern web applications, allo
From playlist OWASP AppSec EU 2013