Cryptography lists and comparisons
List of cryptographers
This is a list of cryptographers. Cryptography is the practice and study of techniques for secure communication in the presence of third parties called adversaries. (Wikipedia).

Cryptography lists and comparisons
This is a list of cryptographers. Cryptography is the practice and study of techniques for secure communication in the presence of third parties called adversaries. (Wikipedia).


Few other Cryptanalytic Techniques
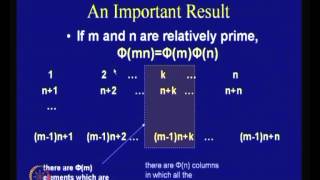
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
From playlist Cryptography
This video gives a general introduction to cryptography WITHOUT actually doing any math. Terms covered include cryptology vs cryptography vs cryptanalysis, symmetric vs public key systems, and "coding theory." NOTE: Yes, I said and wrote "cryptOanalysis" when it's actually "cryptanalysis
From playlist Cryptography and Coding Theory

Public key cryptography - Diffie-Hellman Key Exchange (full version)
The history behind public key cryptography & the Diffie-Hellman key exchange algorithm. We also have a video on RSA here: https://www.youtube.com/watch?v=wXB-V_Keiu8
From playlist Cryptography, Security

How To Create Identity Verification Smart Contract | Session 04 | #ethereum | #blockchain
Don’t forget to subscribe! In this project series, you will learn to create a smart contract for identity verification. This series will cover all the details necessary to teach you how to write a smart contract to verify the identity of a person or an object on the blockchain and ultima
From playlist Create Identity Verification Smart Contract
PMSP - Computational pseudo-randomness and extractors I - Russell Impagliazzo
Russell Impagliazzo UC San Diego and Institute for Advanced Study June 14, 2010 For more videos, visit http://video.ias.edu
From playlist Mathematics

How To Create Coin Market Cap Website Clone In PHP | Session 02 | #blockchain
Don’t forget to subscribe! In this project series, you will learn to create coin market cap website clone in PHP. In this project, you will learn the basics about cryptocurrency and blockchain. You will also learn how to create a cryptocurrency website similar to coin market cap create
From playlist Create Coin Market Cap Website Clone In PHP

Lilya Budaghyan : On APN and AB power functions
CONFERENCE Recording during the thematic meeting : « ALgebraic and combinatorial methods for COding and CRYPTography» the February 23, 2023 at the Centre International de Rencontres Mathématiques (Marseille, France) Filmmaker: Guillaume Hennenfent Find this video and other talks given b
From playlist Combinatorics
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

How To Create Coin Market Cap Website Clone In PHP | Session 02 | #blockchain
Don’t forget to subscribe! In this project series, you will learn how to create a Coin Market Cap website clone in PHP. In this project, you will learn the basics about cryptocurrency and blockchain. You will also learn how to create a cryptocurrency website similar to coin market cap an
From playlist Create Coin Market Cap Website Clone In PHP

OWASP AppSecUSA 2011:How NOT to Implement Cryptography for the OWASP Top 10 (Reloaded)
Speaker: Anthony J. Stieber This talk is an update of a talk in 2008 at the OWASP Minneapolis-St.Paul Chapter which was about encryption as it applies to parts of the OWASP Top Ten. The new talk uses fresh examples of application cryptography successes and failures, and also incorporates
From playlist OWASP AppSecUSA 2011

Ethereum Token Standards | Fungible & Non-fungible Tokens | Session 16 | #ethereum
Don’t forget to subscribe! Ethereum tokens that can be bought, sold, or traded, have become the backbone of the Ethereum ecosystem, innovative companies use them as internal currencies within their ecosystem. Some are listed on exchanges and act like shares of the company and some become
From playlist Fungible & Non-Fungible Tokens

RSA Conference 2010 USA: The Cryptographers Panel 2/6
Clip 2/6 MODERATOR: Ari Juels, Chief Scientist and Director, RSA Laboratories PANELISTS: Whitfield Diffie, Martin Hellman, Ronald Rivest, Adi Shamir, Brian Snow Join the founders of the field for an engaging discussion about the latest advances in cryptography, research areas to wa
From playlist RSA Conference USA 2010

25c3: Chip Reverse Engineering
Speakers: Karsten Nohl, starbug Cryptographic algorithms are often kept secret in the false belief that this provides security. To find and analyze these algorithms, we reverse-engineering the silicon chips that implement them. With simple tools, we open the chips, take pictures, and ana
From playlist 25C3: Nothing to hide

25c3: Full-Disk-Encryption Crash-Course
Speaker: Juergen Pabel Everything to hide This is not a hacking presentation, no vulnerabilities are presented. It's a crash-course in full-disk-encryption ("FDE") concepts, products and implementation aspects. An overview of both commercial and open-source offerings for Windows, Linux,
From playlist 25C3: Nothing to hide

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security