This video gives a general introduction to cryptography WITHOUT actually doing any math. Terms covered include cryptology vs cryptography vs cryptanalysis, symmetric vs public key systems, and "coding theory." NOTE: Yes, I said and wrote "cryptOanalysis" when it's actually "cryptanalysis
From playlist Cryptography and Coding Theory

Introduction - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
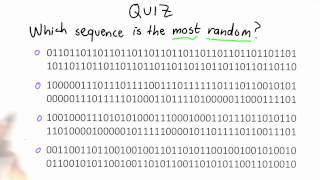
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

28C3: Taking control over the Tor network (en)
For more information visit: http://bit.ly/28C3_information To download the video visit: http://bit.ly/28C3_videos Playlist 28C3: http://bit.ly/28C3_playlist Speakers: Eric Filiol, Seun Omosowon This talk deals with weaknesses identified in the TOR network protocol and cryptography
From playlist 28C3: Behind Enemy Lines

SOURCE Boston 2009: Wireless Sensor Networking As An Asset And A Liability
Speaker: Travis Goodspeed Wireless Sensor Networking (WSN) technology, as typified by Zigbee and ISA100, makes use of ultra-low power microcontrollers and LPAN radios to form self-sufficient networks. A battery-powered network can survive for a year with today's technology, with lifetimes
From playlist Latest uploads

For more information and to download the video visit: http://bit.ly/30C3_info Playlist 30C3: http://bit.ly/30c3_pl Speakers: Nadia Heninger | djb | Tanja Lange This was a busy year for crypto. TLS was broken. And then broken again. Discrete logs were computed. And then computed again.
From playlist 30C3

A brief description of the "Basic Principle" and how it can be used to test for primality.
From playlist Cryptography and Coding Theory

The Year in Post-quantum Crypto
The world is finally catching on to the urgency of deploying post-quantum cryptography: cryptography designed to survive attacks by quantum computers. EVENT: media.ccc.de 2018 SPEAKERS: Daniel J. Bernstein and Tanja Lange PUBLICATION PERMISSIONS: Original video was published with the
From playlist Blockchain

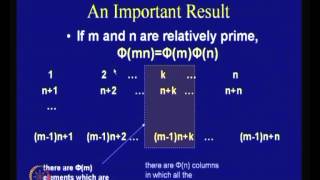
Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Privacy preserving identity verification using third party cloud services and FHE
Speaker - Dr Srinivas Vivek, Open Consent UK and Global Privacy Rights About the event This hybrid conference brought together prominent academics and key players in the field of digital identity from government and industry sectors. The event focused on the socio-technical infrastructu
From playlist Turing trustworthy digital identity international conference 2022

In this session, Cory discusses the tools for using cryptography in Swift, and introduces a new Apple open source project for working with cryptography on all platforms, Swift Crypto. PUBLICATION PERMISSIONS: Original video was published with the Creative Commons Attribution license (reus
From playlist Blockchain

GoRuCo 2013 - Krypt. Semper Pi. by Martin Bosslet
Many people don't like Cryptography. Whenever he falls out of a bar, he carries this strong odor of ivory-towering, bikeshedding and plain, outright arrogance. He seems to be a loner and a smartass, rude, and it's hard to follow his boring, lengthy explanations. But once you get to know hi
From playlist GoRuCo 2013
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

DEFCON 20: Rapid Blind SQL Injection Exploitation with BBQSQL
Speakers: BEN TOEWS SECURITY CONSULTANT, NEOHAPSIS SCOTT BEHRENS SECURITY CONSULTANT, NEOHAPSIS Blind SQL injection can be a pain to exploit. When the available tools work they work well, but when they don't you have to write something custom. This is time-consuming and tedious. This tal
From playlist DEFCON 20


