DSA Algorithm | DSA Algorithm Explained | Digital Signature Algorithm | Simplilearn
In this video on the DSA Algorithm, we learn about the global standard in authentication and verification of digital signatures. We learn about the basics of public key cryptography, and how digital signatures are used in today's internet sphere. Moving on, the origin and specifics of the
From playlist Cyber Security Playlist [2023 Updated]🔥

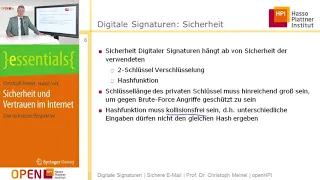
Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Digital Signatures and Digital Certificates
This video explains the purpose of digital signatures and how they work. It begins by reviewing encryption and decryption using an asymmetric pair of keys, and then explains the significance of this when it comes to digital signatures, namely that it doesn’t matter which of the key pair i
From playlist Cryptography

MATH3411 Information, Codes and Ciphers This problem presents digital signatures via the DSS scheme. We are asked to find a public key from a private key, to generate a digital signature, and to check the validity of a received signature. Presented by Thomas Britz, School of Mathematics
From playlist MATH3411 Information, Codes and Ciphers

A high-level explanation of digital signature schemes, which are a fundamental building block in many cryptographic protocols. More free lessons at: http://www.khanacademy.org/video?v=Aq3a-_O2NcI Video by Zulfikar Ramzan. Zulfikar Ramzan is a world-leading expert in computer security and
From playlist Money, banking and central banks | Finance and Capital Markets | Khan Academy

RSA and DSA Encryption Algorithms Explained | Cryptography & Network Security Tutorial | Simplilearn
In today's video on the RSA and DSA encryption algorithms explained, we cover the two most well known symmetric encryption algorithms in our cryptography & network security tutorial. We learn the steps needed to encrypt digital signatures and general data using RSA and DSA algorithms. The
From playlist Cyber Security Playlist [2023 Updated]🔥

RSA Encryption Algorithm | Rivest–Shamir–Adleman | RSA Algorithm Explained | Simplilearn
In this video on the RSA Encryption Algorithm, we learn about the global standard in asymmetric encryption, designed by Rivest-Shamir-Adleman. We understand the basics of asymmetric encryption, handling of digital signatures, and how we can use RSA encryption algorithm in the verification
From playlist Cyber Security Playlist [2023 Updated]🔥

Bitcoin Q&A: "Quantum Supremacy"
Google says it has achieved "quantum supremacy." What does this mean? Is Bitcoin's cryptography now broken? Keep calm, carry on. Chapters 0:00 Google claimed that it has reached quantum supremacy. 2:38 How do you think this will affect mining and the cryptocurrency world in general? 4:41
From playlist Bitcoin Q&A

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live
Mathematics in Cryptography II - Toni Bluher
2018 Program for Women and Mathematics Topic: Mathematics in Cryptography II Speaker: Toni Bluher Affiliation: National Security Agency Date: May 21, 2018 For more videos, please visit http://video.ias.edu
From playlist Mathematics

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live
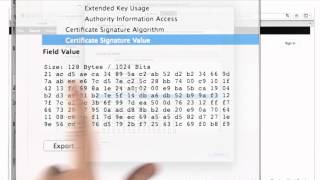
Certificates And Signatures - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cyber Security Interview Questions Part - 5 | Cryptography Interview Questions | Simplilearn
This video on cybersecurity interview questions part 5 focuses on questions from cryptography. This video will walk you through several questions related to encryption, decryption, public key infrastructure, and many more. 🔥Enroll for Free Cyber Security Course & Get Your Completion Certif
From playlist Cyber Security Playlist [2023 Updated]🔥