Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Digital Signature - ElGamal (pt. 3 - Same k Attack)
This video goes over "same k attack" on ElGamal digital signatures. Also see pt.1 (Intro to ElGamal dig. sig) and pt.2 (why ElGamal works), respectively: https://www.youtube.com/watch?v=Jo3wHnIH4y8 https://www.youtube.com/watch?v=cYbJDhTKAXU Questions? Feel free to post them in the comme
From playlist Cryptography and Coding Theory

Digital Signatures - ElGamal (pt.1)
This video introduces the use of ElGamal cryptosystem as type of digital signature. Questions? Feel free to post them in the comments and I'll do my best to answer!
From playlist Cryptography and Coding Theory

Digital Signature - ElGamal (pt. 2)
This video shows why ElGamal digital signatures work with a bit more detail. See ElGamal Digital Signature pt. 1 (which introduces the idea) https://www.youtube.com/watch?v=Jo3wHnIH4y8 Questions? Feel free to post them in the comments and I'll do my best to answer!
From playlist Cryptography and Coding Theory

From playlist Cryptography Lectures

Elliptic Curve ElGamal Cryptosystem
In this video I primarily do through the Elliptic Curve ElGamal crytposystem (Bob's variables/computations, Alice's variables/computations, what is sent, and how it is decrypted by Bob). In addition, I go over the basics of elliptic curves such as their advantages and how they are written.
From playlist Cryptography and Coding Theory

CERIAS Security: Minimizing Trust Liabilities in Secure Group Messaging Infrastructures 1/5
Clip 1/5 Speaker: Himanshu Khurana · University of Illinois at Urbana-Champaign Large-scale collaborative applications are characterized by a large number of users and other processing end entities that are distributed over geographically disparate locations. Therefore, these applicat
From playlist The CERIAS Security Seminars 2005 (1)

From playlist Cryptography Lectures
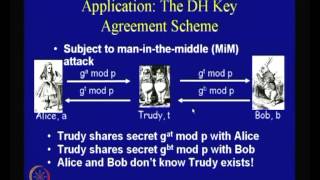
The Diffie-Hellman Problem and Security of ElGamal Systems
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
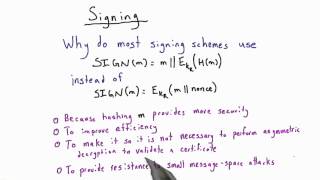
Signing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Digital Signatures: RSA and El Gamal
We describe the theory and applications of digital signatures, and provide two examples of digital signature algorithms: RSA and El Gamal
From playlist PubKey