The Story of Chinese Character :臼
臼 depicts a mortar.
From playlist The Story of HanZi (Chinese Characters)

The Story of Chinese Character :粉
粉 is composed of 米(rice) and 分(to divide). A grain of rice is small, even smaller if divided, so 粉 means powder.
From playlist The Story of HanZi (Chinese Characters)

The Story of Chinese Character :秉
秉 depicts a standing grain(禾) being held by a hand.
From playlist The Story of HanZi (Chinese Characters)

25c3: An introduction to new stream cipher designs
Speaker: Tor E. Bjørstad Turning data into line noise and back Even with "nothing to hide", we want to protect the privacy of our bits and bytes. Encryption is an important tool for this, and stream ciphers are a major class of symmetric-key encryption schemes. Algorithms such as RC4 (us
From playlist 25C3: Nothing to hide

How Encryption Keeps Your Data Safe
Start protecting yourself on the web at https://NordVPN.com/SCISHOW or use code SCISHOW to save 75% off of a 3-year Virtual Private Network plan, plus 1 month free. Keeping our data safe and secure is necessary in today's world, but a lot of the encryption we depend on has been in devel
From playlist Uploads

Cryptography - CS50 for Lawyers 2019
00:00:00 - Introduction 00:00:15 - Cryptography 00:01:25 - Ciphers 00:02:25 - Substitution Cipher 00:09:25 - Caesar Cipher 00:11:08 - Vigenere Cipher 00:17:52 - Substitution Cipher 00:18:20 - Frequency Analysis 00:20:20 - Ciphers (continued) 00:22:20 - Hashes 00:25:46 - Hash Function 00:32
From playlist CS50 for Lawyers 2019

DEFCON 17: Smashing the Stack with Hydra: The Many Heads of Advanced Polymorphic Shellcode
Speakers: Pratap Prabhu Research Assistant, Columbia University Yingbo Song Research Assistant, Columbia University Salvatore. J. Stolfo Professor of Computer Science, Columbia University Recent work on the analysis of polymorphic shellcode engines suggests that modern obfuscation method
From playlist DEFCON 17

Large deviations in periodically driven systems by Grant M Rotskoff
Large deviation theory in statistical physics: Recent advances and future challenges DATE: 14 August 2017 to 13 October 2017 VENUE: Madhava Lecture Hall, ICTS, Bengaluru Large deviation theory made its way into statistical physics as a mathematical framework for studying equilibrium syst
From playlist Large deviation theory in statistical physics: Recent advances and future challenges

25c3: Chip Reverse Engineering
Speakers: Karsten Nohl, starbug Cryptographic algorithms are often kept secret in the false belief that this provides security. To find and analyze these algorithms, we reverse-engineering the silicon chips that implement them. With simple tools, we open the chips, take pictures, and ana
From playlist 25C3: Nothing to hide

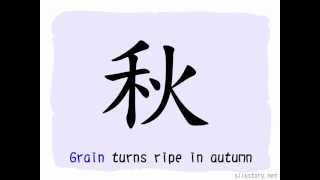
The Story of Chinese Character :禾
禾 depicts a piece of ripe paddy with a ear of grain on the top of it. 禾 is one of the radicals in HanZi.
From playlist The Story of HanZi (Chinese Characters)

The Story of Chinese Character :兼
兼 depicts two standing grains being held by a hand, so 兼 is used to describe the situation of holding more than one stuffs.
From playlist The Story of HanZi (Chinese Characters)

ICO In Depth - Explanation & Analysis | Session 06 | #blockchain
Don’t forget to subscribe! ICO In Depth - Explanation & Analysis This project series is an explanation of ICO and its analysis. This project will try to explain the definition of ICO initial coin offerings, why they are made, and what they accomplish. It will also show viewers what happ
From playlist ICO In Depth - Explanation & Analysis

A Guardian Agent for Secure Delegation
Is SSH (Secure Shell) protocol truly secure? With attributes such as convenience, authentication, and secure encryption, millions of professionals across the globe use SSH to gain remote access to a system without fear of being exposed. But--there are three key issues with SSH that are oft
From playlist ACS/Stanford Computer Forum

Testing a Wooden Barrel Still?? | Moonshiners
Stream Moonshiners on discovery+ ► https://www.discoveryplus.com/show/moonshiners #Moonshiners #Moonshine #DiscoveryChannel Subscribe to Discovery: http://bit.ly/SubscribeDiscovery Follow Us on TikTok: https://www.tiktok.com/@Discovery We're on Instagram! https://instagram.com/Discove
From playlist Moonshiners

BathRuby 2016 - How NEO4J Saved my Relationship by Coraline Ada Ehmke
How NEO4J Saved my Relationship by Coraline Ada Ehmke Relational databases have come a long way in the past decade, but sometimes complex data models (a map of network infrastructure, or a quantum-entangled network of social relationships) call for a different approach. How can we address
From playlist BathRuby 2016