
History of computers - A Timeline
A timeline from the first computer, The Turing Machine, to the 1970's. Hope you guys enjoy,and make sure to subscribe and like! Adding subtitles for our video is welcomed! Your translation can help people around the world see our awesome videos! http://www.youtube.com/timedtext_cs_panel?c
From playlist Computers

What Is the Future of Cryptography?
Historically, as advances were made in the fields of engineering, mathematics, and physics, so the field of cryptography has advanced with them—usually by leaps and bounds. Where is it headed next? Science journalist Simon Singh concedes that the science of secrecy tends to be secret, so w
From playlist Technology

Cryptography: Codes, Ciphers, and Connections
The encryption of information is as old as information itself. Ever since two people wanted to pass something along, so has there been a third party who wanted to be privy to it. This back and forth battle of creating codes, breaking them, and finding new ones has been happening quietly fo
From playlist Mathematics

History of Computers (part 2) - A Timeline
A Timeline Following after the 1970's comes the 1980's we will go all the way up to the 1990's This is the most exciting part of computer history yet. Sorry that we haven't posted in a while a loooooong while..... hope ya like this vid and we'll try our best to shorten the time:D Make
From playlist Computers
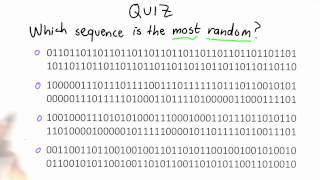
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

Public key cryptography - Diffie-Hellman Key Exchange (full version)
The history behind public key cryptography & the Diffie-Hellman key exchange algorithm. We also have a video on RSA here: https://www.youtube.com/watch?v=wXB-V_Keiu8
From playlist Cryptography, Security

Overview on Modern Cryptography
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Mathematics in Post-Quantum Cryptography - Kristin Lauter
2018 Program for Women and Mathematics Topic: Mathematics in Post-Quantum Cryptography Speaker: Kristin Lauter Affiliation: Microsoft Research Date: May 21, 2018 For more videos, please visit http://video.ias.edu
From playlist My Collaborators

2022 I E Block Community Lecture: AI and Cryptography
July 13, 2022 How is Artificial Intelligence (AI) changing your life and the world? How can you expect your data to be kept secure and private in an AI-driven future? Kristin Lauter of Meta AI Research gives the I. E. Block Community Lecture titled "Artificial Intelligence and Cryptograph
From playlist SIAM Conference Videos
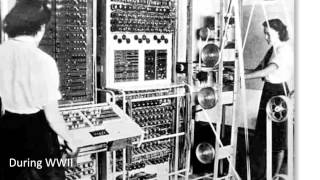
Colossus - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Bitcoin Q&A: Schnorr Signatures and the Privacy Roadmap
How important are privacy improvements to Bitcoin in the roadmap? How will second layers and atomic swaps help with this? When will Schnorr signatures / signature aggregation be added to Bitcoin? What are Taproot and Graftroot? Will it be done through a soft or hard fork? Should we keep tr
From playlist Privacy and Surveillance

IMS Public Lecture: Are Quantum Computers The Next Generation Of Supercomputers?
Reinhard Werner, Technische Universität Braunschweig, Germany
From playlist Public Lectures

“As soon as you’ve got something precious to hide, someone will want to steal it.” Science journalist Simon Singh sheds light on the dark nature of cryptography. He explains just how far back the field of cryptography goes, and just how long it has taken for even some of the simplest ciphe
From playlist Technology

Stanford Seminar - Evolution of a Web3 Company
This talk was given the week of October 3, 2022. Guest speaker: Sam Green, Co-Founder & Head of Research at Semiotic Labs. #web3

Katherine E. Stange: Ring learning with errors and rounding
CIRM HYBRID EVENT Among the main candidates for post-quantum cryptography are systems based on the Ring Learning with Errors and Ring Learning with Rounding problems. I’ll give an overview of the number theory involved in these problems and try to persuade you to join in cryptanalyzing th
From playlist Number Theory

WTF Are Paradoxes & How Do They Mess Up Time Travel?
Episode 3 of 4 Check us out on Soundcloud! https://soundcloud.com/dnewsplus Please Subscribe! http://bit.ly/28iQhYC Discovery GO - http://smart.link/57ae195b47796 Science GO - http://smart.link/57ae1a34dd168 Every cause has an effect. What were to happen if we could successf
From playlist Have We Already Time Traveled?

Open Source Computer Science Degree
In this video, I will be taking you through the various resources that make up the open-source computer science degree. The OSSU curriculum is a complete education in computer science using online materials. It's not merely for career training or professional development. It's for those wh
From playlist Ethical Hacking & Penetration Testing - Complete Course

For more information and to download the video visit: http://bit.ly/30C3_info Playlist 30C3: http://bit.ly/30c3_pl Speakers: Nadia Heninger | djb | Tanja Lange This was a busy year for crypto. TLS was broken. And then broken again. Discrete logs were computed. And then computed again.
From playlist 30C3

Bitcoin Q&A: Proof-of-work Changes
What do you think about a Bitcoin proof-of-work algorithm change to combat mining centralisation like Monero did? Is ASIC-resistance futile? Is a hard fork still a valid option in case of an emergency? Chapters 0:00 What are your thoughts on a Bitcoin proof-of-work change to combat mining
From playlist English Subtitles - aantonop Videos with subtitles in English