Weak Ciphers - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain

Weak PRNGs - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain

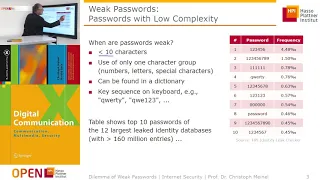
Why creating a strong password really matters
What is a “strong password”, exactly? What are some ways that you can create a password that is strong and easy to remember?
From playlist Internet Safety

OWASP AppSecUSA 2011:How NOT to Implement Cryptography for the OWASP Top 10 (Reloaded)
Speaker: Anthony J. Stieber This talk is an update of a talk in 2008 at the OWASP Minneapolis-St.Paul Chapter which was about encryption as it applies to parts of the OWASP Top Ten. The new talk uses fresh examples of application cryptography successes and failures, and also incorporates
From playlist OWASP AppSecUSA 2011

GoGaRuCo 2012 - Modern Cryptography
Modern Cryptography by: John Downey Once the realm of shadowy government organizations, cryptography now permeates computing. Unfortunately, it is difficult to get correct and most developers know just enough to be harmful for their projects. Together, we’ll go through the basics of moder
From playlist gogaruco 2012

Cryptography - Seminar 1 - Foundations
This seminar series is about the mathematical foundations of cryptography. In the first seminar Eleanor McMurtry introduces cryptography and explains some of the problems that need to be solved in order to develop proper foundations. The webpage for this seminar is https://lnor.net/uc-sem
From playlist Metauni

Hacktivity 2010: The History of the Hungarian Cryptography
Speaker: Dr. István Szabó
From playlist Hacktivity 2010

26C3: Yes We Cant - on kleptography and cryptovirology 5/6
Clip 5/6 Speaker: Moti Yung In this talk I will survey some of the results (with Adam Young) on Cryptovirology (the art of employing public key cryptography maliciously as part of a malware attack, such as in ransomware) and the related Kleptography (the art of embedding cryptographic
From playlist 26C3: Here be dragons day 3

The History of Cryptography: Block Cyphers, Stream Cyphers, Public Keys and more!
Alice and Bob have secrets they want to talk about without Eve being able to listen in. Worse yet, the mischievous Mallory delights in changing messages sent between parties. In such a hostile environment how can Alice talk to Bob without their messages being overheard and how can she be
From playlist Talks

Proving Security Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Types of Cryptography Algorithms | Cryptography in Network Security | Edureka | Cybersecurity Live-2
🔥Edureka Cybersecurity Online Training: https://www.edureka.co/cybersecurity-certification-training This Edureka video on Cryptography Algorithms Explained talks about the various algorithms used for cryptography and how they help in making our data secure. Cybersecurity Training Playlist
From playlist Edureka Live Classes 2020

Adeline Roux-Langlois : Using structured variants in lattice-based cryptography - Lecture 1
CONFERENCE Recording during the thematic meeting : « Francophone Computer Algebra Days» the March 06, 2023 at the Centre International de Rencontres Mathématiques (Marseille, France) Filmmaker: Jean Petit Find this video and other talks given by worldwide mathematicians on CIRM's Audiov
From playlist Mathematical Aspects of Computer Science

The Year in Post-quantum Crypto
The world is finally catching on to the urgency of deploying post-quantum cryptography: cryptography designed to survive attacks by quantum computers. EVENT: media.ccc.de 2018 SPEAKERS: Daniel J. Bernstein and Tanja Lange PUBLICATION PERMISSIONS: Original video was published with the
From playlist Blockchain

Proving Security - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Symmetric Key Cryptography: Cryptographic Techniques
This is the fifth in a series about cryptography; an extremely important aspect of computer science and cyber security. It reviews how the XOR logical operation can be used to encrypt at the bit level in symmetric key cryptography, then shows how this can be combined with permutation step
From playlist Cryptography