Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

EEVBlog #1131 - £1M Prank - Banksy Artwork Shredded! HOW?
A look at how the Banksy artwork prank "Girl with a Balloon" shredded itself moments after being sold for £1M at a Sotheby's auction. How long did it sit idle waiting to be triggered?, and was this actually possible? NOTE: The Artwork was authenticated by "Pest Control", which is Banksy's
From playlist Debunking

EEVblog #1136 - Banksy Artwork Shredder - Part 2 (Still Trolling!)
Banksy posted an update video showing more of the prank build and the shredding mechanism. But he's still trolling us! Banky's Directors Cut video: https://www.youtube.com/watch?v=vxkwRNIZgdY Forum: http://www.eevblog.com/forum/blog/eevblog-1136-banksy-artwork-shredder-part-2-(still-trol
From playlist Electronics Design / Build

Correctness And Security - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Klein-Gordon equation on discrete lattice by Iveta Semorádová
DATE: 04 June 2018 to 13 June 2018 VENUE:Ramanujan Lecture Hall, ICTS Bangalore Non-Hermitian Physics-"Pseudo-Hermitian Hamiltonians in Quantum Physics (PHHQP) XVIII" is the 18th meeting in the series that is being held over the years in Quantum Physics. The scope of the program on Non-H
From playlist Non-Hermitian Physics - PHHQP XVIII

ShmooCon 2013: Crypto: You're Doing It Wrong
For more information and to download the video visit: http://bit.ly/shmoocon2013 Playlist ShmooCon 2013: http://bit.ly/Shmoo13 Speaker: Ron Bowes As a group. the security industry has solved a lot of difficult problems. Firewalls do a great job blocking traffic, overflow vulnerabilities
From playlist ShmooCon 2013

26C3: Exposing Crypto Bugs through reverse engineering 3/5
Clip 3/5 Speaker: Philippe Oechslin Breaking good crypto is hard. It takes a genius to find a flaw in AES or Blowfish. On the other hand, it is also difficult to program cryptography correctly. Thus the simpler way of breaking a cryptographic software is often to reverse engineer it a
From playlist 26C3: Here be dragons day 1

ShmooCon 2014: Genuinely "Trusted Computing:" Free and Open Hardware Security Modules
For more information visit: http://bit.ly/shmooc14 To download the video visit: http://bit.ly/shmooc14_down Playlist Shmoocon 2014: http://bit.ly/shmooc14_pl Speaker: Ryan Lackey "Trusted Computing" unfortunately often means trusting a black box provided by a third party who may not be p
From playlist ShmooCon 2014

Libre Not Libra: Facebook's Blockchain Project
In this talk, Andreas answers the burning question... has he tried haggis? Just kidding. What should we make of Facebook's Libra whitepaper? Will it survive to become a production network? Why is Silicon Valley coming for banking? Does it change anything about the regulatory environment fa
From playlist Blockchain

Is coding really dead? 6 trends that look bad
Some people say programming is a dying skill, but is this prediction accurate? Let's look at 6 trends in tech that don't look good for coders. #programming #tech #learntocode 💬 Chat with Me on Discord https://discord.gg/fireship 🔗 Resources Coding is Dead by @TechLead https://youtu.
From playlist Top N Lists

How does cryptography ACTUALLY work?
In this video I'll attempt to introduce you to some of the maths behind modern cryptography, which is in a sense how the world around us works now. Surprisingly, it has a lot to do with the simple ideas of division and remainders. We'll cover modular arithmetic basics, continued fractions
From playlist Summer of Math Exposition Youtube Videos

int0x80 (of Dual Core) -- Anti-Forensics for the Louise
All videos at: http://www.irongeek.com/i.php?page=videos/derbycon1/mainlist
From playlist DerbyCon 2011

Libre Not Libra: Facebook's Blockchain Project
In this talk, Andreas answers the burning question... has he tried haggis? Just kidding. What should we make of Facebook's Libra whitepaper? Will it survive to become a production network? Why is Silicon Valley coming for banking? Does it change anything about the regulatory environment fa
From playlist English Subtitles - aantonop Videos with subtitles in English
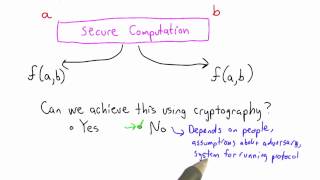
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Beginner’s Guide #1: Andreas M. Antonopoulos on Why We Need Bitcoin
In this interview, I talk to Andreas M. Antonopoulos; speaker and best selling author of Mastering Bitcoin and an unrivalled Bitcoin evangelist. Andreas explains why the current monetary system is no longer fit for purpose and why Bitcoin is the answer. WHERE TO FIND THE SHOW → My website
From playlist Interviews and Shows

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain