An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

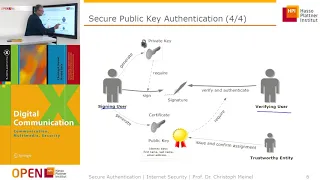
Trusted Third Party Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Encryption and HUGE numbers - Numberphile
Banks, Facebook, Twitter and Google use epic numbers - based on prime factors - to keep our Internet secrets. This is RSA public-key encryption. More links & stuff in full description below ↓↓↓ Gold Vault: https://youtu.be/CTtf5s2HFkA This video features Dr James Grime (http://singingban
From playlist Computer stuff on Numberphile

Back To Signatures Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

One Time Pad - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Embedded Recipes 2018 - WooKey: the USB Battlefront Warrior - Mathieu Renard, Ryad Benadjila
USB devices are nowadays ubiquitous and participate to a wide variety of use cases. Recent studies have exposed vulnerabilities on the USB implementations, and among them the BadUSB attacks are a serious threat against the integrity of USB devices. Firmwares, hosts Operating Systems, as we
From playlist Embedded Recipes 2018

DEFCON 16: Generic, Decentralized, Unstoppable Anonymity: The Phantom Protocol
Speaker: Magnus Bråding, Security Researcher, Fortego Security Recent years, and especially this past year, have seen a notable upswing in developments toward anti online privacy around the world, primarily in the form of draconian surveillance and censorship laws (both passed and attempt
From playlist DEFCON 16

DeepSec 2013: Mobile Fail: Cracking Open "Secure" Android Containers
For more information and to download the video visit: http://bit.ly/DS13_info Playlist Deepsec 2013: http://bit.ly/DS13_pl Slides: http://bit.ly/1bZeVhO Speaker: Chris John Riley Chris John Riley explains the security of Android containers on mobile phones. His presentation was held at D
From playlist DeepSec 2013

Keeping Secrets: Cryptography In A Connected World
Josh Zepps, Simon Singh, Orr Dunkelman, Tal Rabin, and Brian Snow discuss how, since the earliest days of communication, clever minds have devised methods for enciphering messages to shield them from prying eyes. Today, cryptography has moved beyond the realm of dilettantes and soldiers to
From playlist Explore the World Science Festival
How Companies Lie To You About End-to-End Encryption
This is a talk with realguyman, a privacy researcher and a contributor to privacyguides.org. https://github.com/orgs/privacyguides/people#member-realguyman Support independent research and analysis by joining my Patreon page: https://www.patreon.com/thehatedone Timestamps 00:00:00 Intro
From playlist Talks, interview and podcasts

NOTACON 5: Data Loss Protection - Hope or Hype?
Speakers: Enno Rey and Angus Blitter To lose control over one's own data is one of the primal fears of the digital age. More than ever this applies in particular to the world of corporations and organizations with all their trade secrets and peachy marketing plans to be protected from lea
From playlist Notacon 5

How To Run Nginx In Docker Container on Ubuntu | Session 11 | #programming
Don’t forget to subscribe! In this project series, you will learn how to run Nginx in Docker container on Ubuntu. This tutorial will cover all the steps to running an Nginx container on docker on ubuntu16. In this tutorial, you will learn how to configure Nginx to your web application.
From playlist Run Nginx In Docker Container on Ubuntu

The Quantum Revolution: Shohini Ghose Public Lecture
In her live public lecture at Perimeter Institute on March 4, 2020, Shohini Ghose – professor of physics and computer science at Wilfrid Laurier University, President of the Canadian Association of Physicists, and TED Senior Fellow – guided the audience through the latest advances in the q
From playlist Public Lecture Series

Presented by WWCode Blockchain Speaker: Swetha Srinivasan, Google This talk will give an overview of introductory concepts in security such as confidentiality, integrity, availability, authentication and authorization. It will cover how cryptography is used in real world systems and funda
From playlist Center for Applied Cybersecurity Research (CACR)

Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography

The History of Cryptography: Block Cyphers, Stream Cyphers, Public Keys and more!
Alice and Bob have secrets they want to talk about without Eve being able to listen in. Worse yet, the mischievous Mallory delights in changing messages sent between parties. In such a hostile environment how can Alice talk to Bob without their messages being overheard and how can she be
From playlist Talks