
Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
This video gives a general introduction to cryptography WITHOUT actually doing any math. Terms covered include cryptology vs cryptography vs cryptanalysis, symmetric vs public key systems, and "coding theory." NOTE: Yes, I said and wrote "cryptOanalysis" when it's actually "cryptanalysis
From playlist Cryptography and Coding Theory

Network Security, Part 2 : Public Key Encryption
Fundamental concepts of public key encryption are discussed. RSA encryption method explained with an example. Confidentiality of message is presented.
From playlist Cryptography, Security

25c3: Full-Disk-Encryption Crash-Course
Speaker: Juergen Pabel Everything to hide This is not a hacking presentation, no vulnerabilities are presented. It's a crash-course in full-disk-encryption ("FDE") concepts, products and implementation aspects. An overview of both commercial and open-source offerings for Windows, Linux,
From playlist 25C3: Nothing to hide

Cyber Security Full Course 2023 | Cyber Security Course Training For Beginners 2023 | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CyberSecurityFullCourse2023-hXSFdwIOfnE&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.
From playlist Cyber Security Playlist [2023 Updated]🔥

Ethical Hacking Full Course | Ethical Hacker Course For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseNov16-VL5261WGa70&utm_medium=DescriptionFF&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_ca
From playlist Simplilearn Live

CAS1219 Our Storage Journey Migrating VMware onto SUSE Enterprise Storage SES
This case study session was delivered at SUSECON in April 2019, in Nashville, TN. Abstract: We will discuss our journey, researching Ceph and SUSE Enterprise Storage including our progress over the last 18 months. Starting with our hardware decisions and why, the installation of the syst
From playlist SUSECON 2019

Ethical Hacking Full Course 2022 | Ethical Hacking Course For Beginners 2022 | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseJan7&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_campaig
From playlist Simplilearn Live

DEFCON 19: Hacking .Net Applications: The Black Arts
Speaker: Jon McCoy DigitalbodyGuard This presentation will cover the Black Arts of making Cracks, KeyGens, Malware, and more. The information in this presentation will allow a .NET programmer to do unspeakable things .NET applications. I will cover the life cycle of developing such attack
From playlist DEFCON 19

Kali Linux For Ethical Hacking | Kali Linux For Beginners 2023 | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=KaliLinuxForEthicalHacking-I2CrZkViM9M&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecu
From playlist Ethical Hacking Playlist [2023 Updated] 🔥
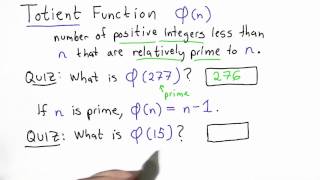
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

29C3: (Un)Sicherheit Hardware-basierter Festplattenverschlüsselung (DE)
Speaker: tilo Hardware-basierte Festplattenvollverschlüsselungen in Form sogenannter SEDs (Self-Encrypting Drives) werden gemeinhin als sichere und performante Alternative zu Software-basierter Verschlüsselung wie BitLocker und TrueCrypt gesehen. Während der Performance-Gewinn und die Ben
From playlist 29C3: Not my department

Public Key Cryptography & RSA: Part 1
Fundamental concepts of Public Key Encryption are discussed. RSA Public Encryption is presented. Optimization of Private Key operations is analyzed. Public Key Encryption Symmetric vs. Public-Key RSA Public Key Encryption RSA Key Construction Optimizing Private Key Operations RSA Securit
From playlist Network Security

For more information and to download the video visit: http://bit.ly/30C3_info Playlist 30C3: http://bit.ly/30c3_pl Speakers: Nadia Heninger | djb | Tanja Lange This was a busy year for crypto. TLS was broken. And then broken again. Discrete logs were computed. And then computed again.
From playlist 30C3

