
A USB drive is a small, removable hard drive that plugs into a USB port on your computer. To learn more about USB Drives visit: https://edu.gcfglobal.org/en/computerbasics/bringing-your-files-with-you/1/ We hope you enjoy!
From playlist Computer Basics

EnCase Computer Forensics Demo
This is a short demo of EnCase I worked up. If you are interested in some of what professional computer forensics software can do then this is for you.
From playlist digital forensics

Private Messages Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

How External Hard Drives Are Made! | How It's Made | Science Channel
An inside look at how external hard drives are made! #howitsmade #sciencechannel Stream How It's Made: https://www.discoveryplus.com/show/how-its-made About How It's Made: Explore the fascinating world of how everyday items are manufactured and produced. From aluminum foil to contact len
From playlist Recent Uploads

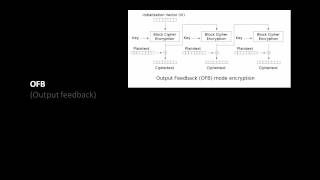
Encrypt Outputs - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Bitcoin Q&A: Key Storage Best Practices
What is a hierarchical deterministic (HD) wallet? How are paper wallets different from hardware wallets? Which of the Bitcoin wallets and / or clients (mobile, desktop, hardware) is best for storing coins? Are hardware wallets with Bluetooth secure? Regarding desktop wallets, what happens
From playlist English Subtitles - aantonop Videos with subtitles in English

Cfb Decryption Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Hashing And EKE - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Backup Special: Save Your Data!!! When To Backup, 3-2-1 Backups, Arch: 360TB, 13 Billion Years!
5D Data Storage on Quartz Glass Lasts 13 Billion Years?!? Backup Special, Save Your Data! When To Backup, 3-2-1 Backups ☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆☆ When To Back Up @ngageguy tweets, "After my HD failure I tweeted to you not long ago, I would suggest you give your listeners some tips
From playlist Ancient Advanced Civilizations Playlist
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

The Complete VeraCrypt Encryption Tutorial
Hey guys! HackerSploit here back again with another video, in this video, I will be showing you how to use VeraCrypt to create encrypted volumes and how to encrypt drives. Links Used In Video: https://veracrypt.ft/en/ Our Platforms: Hsploit: https://hsploit.com/ HackerSploit Forum: https
From playlist Ethical Hacking & Penetration Testing - Complete Course

Kali Linux For Ethical Hacking | Kali Linux For Beginners 2023 | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=KaliLinuxForEthicalHacking-I2CrZkViM9M&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecu
From playlist Ethical Hacking Playlist [2023 Updated] 🔥

Embedded Recipes 2018 - WooKey: the USB Battlefront Warrior - Mathieu Renard, Ryad Benadjila
USB devices are nowadays ubiquitous and participate to a wide variety of use cases. Recent studies have exposed vulnerabilities on the USB implementations, and among them the BadUSB attacks are a serious threat against the integrity of USB devices. Firmwares, hosts Operating Systems, as we
From playlist Embedded Recipes 2018

Ethical Hacking Full Course | Ethical Hacker Course For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseNov16-VL5261WGa70&utm_medium=DescriptionFF&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_ca
From playlist Simplilearn Live

Cyber Security Full Course 2023 | Cyber Security Course Training For Beginners 2023 | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CyberSecurityFullCourse2023-hXSFdwIOfnE&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.
From playlist Cyber Security Playlist [2023 Updated]🔥

OWASP AppSecUSA 2011: CloudSec 12-Step
Speaker: Adrian Lane Do you think cloud security is mainframe computing all over again? Is Azure security just like Windows security? If so, then join me for CloudSec Anonymous, a 12-step program for those of you who want to understand what's different about cloud security. This presentat
From playlist OWASP AppSecUSA 2011

Organize Google Drive with Colors and Icons 🗂️
Google Drive is fantastic for managing all of your files and folders. But you don’t have to be bland and organize Drive by name only. Get creative and start adding colors to help you identify key folders. And don’t stop there. Add emoji’s and icons to differentiate your folders within Goog
From playlist Google Drive


