
Key Distribution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Key Management & Distribution: Part 1
Fundamental concepts of Distribution of public & private keys are discussed. PKI and PKIX are analyzed. Digital certificates standards are presented
From playlist Network Security

Pairwise Distribution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Pairwise Distribution Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Primitive Roots - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Pseudorandom Number Generation and Stream Ciphers
Fundamental concepts of Pseudorandom Number Generation are discussed. Pseudorandom Number Generation using a Block Cipher is explained. Stream Cipher & RC4 are presented.
From playlist Network Security

More videos like this online at http://www.theurbanpenguin.com Now that we have a keyserver to send to we can look at how we generater a gpg key pair and distribute the public key to the keyserver with gpg --send-key
From playlist LPIC-3

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Jonathan Katz - Introduction to Cryptography Part 1 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography I" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This lecture will serve as a "crash course" in modern cryptography for those with no prior exposure
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

0:15 - Review 2:29 - Learning objectives 2:48 - 1. Construct and interpret sampling distributions using StatKey 3:36 - StatKey 10:42 - Review of terms 12:12 - 2. Explain the general form of a confidence interval 16:59 - 3. Interpret a confidence interval 23:47 - 4. Explain the
From playlist STAT 200 Video Lectures

Stanford Seminar - Distributional Representations and Scalable Simulations for Real-to-Sim-to-Real
Distributional Representations and Scalable Simulations for Real-to-Sim-to-Real with Derformables Rika Antonova April 22, 2022 This talk will give an overview of: - the challenges with representing deformable objects - a distributional approach to state representation for deformables - Re
From playlist Stanford AA289 - Robotics and Autonomous Systems Seminar

Live CEOing Ep 65: New Language Design in Wolfram Language
Watch Stephen Wolfram and teams of developers in a live, working, language design meeting. This episode is about New Language Design in the Wolfram Language.
From playlist Behind the Scenes in Real-Life Software Design

Foundations for Learning in the Age of Big Data IV - Maria Florina Balcan
2022 Program for Women and Mathematics: The Mathematics of Machine Learning Topic: Foundations for Learning in the Age of Big Data II Speaker: Maria Florina Balcan Affiliation: Carnegie Mellon University Date: May 24, 2022 Balcan-2022-05-27
From playlist Mathematics

Introduction To Apache Cassandra Certification Training | Simplilearn
The Apache Cassandra tutorial gives you an overview of Apache Cassandra which comprises of overview of big data, NoSQL database, Apache Cassandra Architecture. 🔥Explore Our Free Courses: https://www.simplilearn.com/skillup-free-online-courses?utm_campaign=ApacheCassandra&utm_medium=Descrip
From playlist Big Data Hadoop Tutorial Videos | Simplilearn [2022 Updated]

Blockchain Technology Explained (2 Hour Course)
Blockchain Technology Course will cover: - Technology overview - Blockchain evolution - Decentralized web - Distributed organizations - Distributed ledger - Smart contracts - Distributed applications - Internet of value - Token economies **** INTERESTED IN THE STOCK MARKET? I developed a
From playlist Blockchain
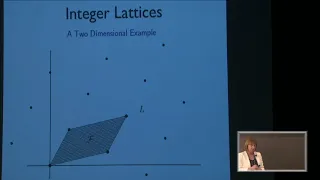
Mathematical Ideas in Lattice Based Cryptography - Jill Pipher
2018 Program for Women and Mathematics Topic: Mathematical Ideas in Lattice Based Cryptography Speaker: Jill Pipher Affiliation: Brown University Date: May 21, 2018 For more videos, please visit http://video.ias.edu
From playlist Mathematics

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Secret Sharing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Jonathan Katz - Introduction to Cryptography Part 2 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography II" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This session will focus on public-key cryptography, including key exchange, public-key encryption,
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography