
Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Cryptanalysis of Classical Ciphers
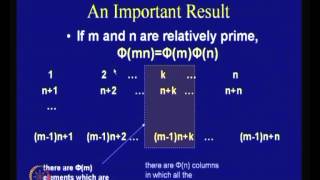
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security
PCP and Delegating Computation: A Love Story - Yael Tauman Kalai
Computer Science/Discrete Mathematics Seminar I Topic: PCP and Delegating Computation: A Love Story Speaker: Yael Tauman Kalai Affiliation: Microsoft Research Date: January 28, 2019 For more video please visit http://video.ias.edu
From playlist Mathematics

Jonathan Katz - Introduction to Cryptography Part 1 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography I" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This lecture will serve as a "crash course" in modern cryptography for those with no prior exposure
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

This lecture is an informal introduction to the P=NP question in computer science: are nondeterministic polynomial time problems (NP) the same as polynomial time problems (P)? We describe what these terms mean, give a brief history, and examine some of the arguments for and against this qu
From playlist Math talks

Zero Knowledge Proofs - Seminar 5 - NP languages have zero knowledge proofs
This seminar series is about the mathematical foundations of cryptography. In this series Eleanor McMurtry is explaining Zero Knowledge Proofs (ZKPs). This seminar covers the 1991 proof by Goldreich-Micali-Widgerson that every NP language has a zero knowledge proof. You can join this semi
From playlist Metauni

Lecture 28: Random Numbers - Richard Buckland UNSW (2008)
Extension lecture introducing randomness. What is a random process? How can a deterministic process on a deterministic computer generate random output? Why is randomness useful? What are problems we face when generating random numbers? The lecture introduces Von Neumann's simple algori
From playlist CS1: Higher Computing - Richard Buckland UNSW

Bitcoin Q&A: Key Storage Best Practices
What is a hierarchical deterministic (HD) wallet? How are paper wallets different from hardware wallets? Which of the Bitcoin wallets and / or clients (mobile, desktop, hardware) is best for storing coins? Are hardware wallets with Bluetooth secure? Regarding desktop wallets, what happens
From playlist English Subtitles - aantonop Videos with subtitles in English

Encryption Explained Simply | What Is Encryption? | Cryptography And Network Security | Simplilearn
In today's video on encryption explained simply, we take a look at why cryptography is essential when it comes to protecting our privacy on the internet. We take a look at how what is encryption, how encryption and decryption works with simple step by step explanation, and move onto it's c
From playlist Cyber Security Playlist [2023 Updated]🔥

Rocky Mountain Ruby 2014 - 80,00 Plaintext Passwords
fluffmuffin, peppercorn, gilligan — those are just a few of our users' plaintext passwords. I have 80,000 more, and it only took me 87 seconds to gather them from our customer database in a white-hat attack. In Act I, we'll cover the history of secure password storage, examine the hack,
From playlist Rocky Mountain Ruby 2014

IMT4889: Evaluation of messaging protocols
IMT4889 - Specialisation in Decentralised Technologies Evaluation of messaging protocols
From playlist 2021 - IMT4889 - Decentralisation
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Jonathan Katz - Introduction to Cryptography Part 2 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography II" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This session will focus on public-key cryptography, including key exchange, public-key encryption,
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

