Secret Sharing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
SSH Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Storing Passwords Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

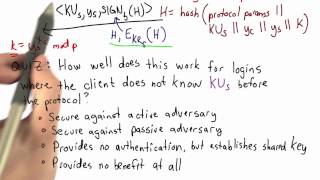
Hashing And EKE - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Public Key Cryptography: Diffie-Hellman Key Exchange (short version)
This is a segment of this full video: https://www.youtube.com/watch?v=YEBfamv-_do Diffie-Hellman key exchange was one of the earliest practical implementations of key exchange within the field of cryptography. It relies on the discrete logarithm problem. This test clip will be part of the
From playlist Cryptography, Security

Lec 23 | MIT 6.033 Computer System Engineering, Spring 2005
Authorization and Confidentiality View the complete course at: http://ocw.mit.edu/6-033S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.033 Computer System Engineering, Spring 2005

EKE Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
OpenSSH Internals for PowerShell Pros by Anthony Nocentino In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd config
From playlist PowerShell + DevOps Global Summit 2018

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd configuration, and troubleshooting methods when things go wrong!
From playlist PowerShell + DevOps Global Summit 2018

PowerShell+ 2019 - Firewall Evasion and Remote Access with OpenSSH by Anthony Nocentino
OpenSSH is much more than just remote terminal access to servers, it provides a full suite of remote connectivity methods to your network and its services. In this session, we will look at how to use OpenSSH and its forwarding, tunneling and VPN capabilities so that we can reach securely r
From playlist PowerShell + DevOps Global Summit 2019

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live

RailsConf 2017: The Art & Craft of Secrets: Using the Cryptographic Toolbox by Michael Swieton
RailsConf 2017: The Art & Craft of Secrets: Using the Cryptographic Toolbox by Michael Swieton Picking an encryption algorithm is like choosing a lock for your door. Some are better than others - but there's more to keeping burglars out of your house (or web site) than just the door lock
From playlist RailsConf 2017

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live

PGConf NYC 2021 - Get Your Insecure PostgreSQL Passwords to SCRAM! by Jonathan S. Katz
Get Your Insecure PostgreSQL Passwords to SCRAM! by Jonathan S. Katz Passwords: they just seem to work. You connect to your PostgreSQL database and you are prompted for your password. You type in the correct character combination, and presto! you're in, safe and sound. But what if I tol
From playlist PGConf NYC 2021

Cyber Security Training For Beginners | Cyber Security Tutorial | #LearningMarathon2021 |Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CyberSecurity-54YCY8_vB2U&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-
From playlist Simplilearn Live