Comprise a system, dump the hashes and uses them in the future! Video made by: pauldotcom.com
From playlist 62 - Category - exploit videos

In this video, you’ll learn more about how hashtags are used on Twitter. Visit https://www.gcflearnfree.org/twitter/what-is-a-hashtag/1/ for our text-based lesson. This video includes information on: • Using hashtags • Browsing popular hashtags We hope you enjoy!
From playlist Twitter

Learn how to read key-value pairs from a text file into a HashMap.
From playlist Intermediate Java

https://en.wikipedia.org/wiki/SHA-1#Examples_and_pseudocode If you have any questions of want to contribute to code or videos, feel free to write me a message on youtube or get my contact in the About section or googling my contacts.
From playlist Programming

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

What's a hash and what's the point?
http://passwordsgenerator.net/sha256-hash-generator/ If you have any questions of want to contribute to code or videos, feel free to write Nikolaj Kuntner a message on youtube or get my contact in the About section or googling my contacts.
From playlist Programming

Provide Scarcity Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Hash Tables - Beau teaches JavaScript
Hash tables are a quick way to implement associative arrays, or mappings of key-value pairs. Find our more and learn how to create one in JavaScript. 💻 Code: http://codepen.io/beaucarnes/pen/VbYGMb?editors=0012 🔗 Info: http://www.willvillanueva.com/javascript-hash-tables/ 🐦 Beau Carnes
From playlist Data Structures and Algorithms - Beau teaches JavaScript

Take instructor-led Live class on Java Tutorial at: http://www.edureka.co/java-course The following topics were covered in this Java Tutorial: Input and Output Streams, Arrays List, Methods in Arraylist, Traversing an Arraylist, Iterator, Enumeration, List Iterator, Scanner, Bufferedread
From playlist Java Online Training Videos

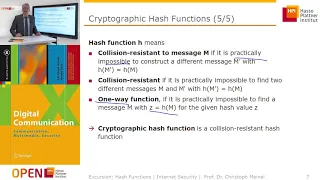
Top Hashing Algorithms In Cryptography | MD5 and SHA 256 Algorithms Explained | Simplilearn
In this video on Top Hashing Algorithms In Cryptography, we will cover the technical aspects of hashing while going through some well-known hash functions and algorithms at the end. We cover the basics of cryptography and its applications. We also have detailed MD5 and SHA265 Explained sec
From playlist Cyber Security Playlist [2023 Updated]🔥

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live

SHA 256 | SHA 256 Algorithm Explanation | How SHA 256 Algorithm Works | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=SHA256&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_campai
From playlist Big Data Hadoop Tutorial Videos For Beginners [2022 Updated]

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live

ArrrrCamp 2015 - Ruby keyword args and the options hash, from the parser to the virtual machine
By Étienne Barrié Ruby has slowly but surely added support for keyword arguments. Starting from the implicit braces for a hash at the end of an argument list, it has grown up to required keyword arguments in 2.1. This talk will try to convince you that keyword arguments are a lie and don't
From playlist ArrrrCamp 2015

From playlist CS50 Walkthroughs

From playlist CS50 Walkthroughs 2012