DevOpsDays NYC 2016 - Post-Quantum DevOps by Nick Doiron
DevOpsDays NYC 2016 - Post-Quantum DevOps by Nick Doiron In the past year Google, the NSA, and NIST have urged developers and theorists to get more serious about quantum computing. What are quantum computers, do they exist, and if so, how do we keep stuff secret from them? How does this c
From playlist DevOpsDays NYC 2016

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

The Year in Post-quantum Crypto
The world is finally catching on to the urgency of deploying post-quantum cryptography: cryptography designed to survive attacks by quantum computers. EVENT: media.ccc.de 2018 SPEAKERS: Daniel J. Bernstein and Tanja Lange PUBLICATION PERMISSIONS: Original video was published with the
From playlist Blockchain

A Tutorial on Network Protocols
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Mathematics in Post-Quantum Cryptography - Kristin Lauter
2018 Program for Women and Mathematics Topic: Mathematics in Post-Quantum Cryptography Speaker: Kristin Lauter Affiliation: Microsoft Research Date: May 21, 2018 For more videos, please visit http://video.ias.edu
From playlist My Collaborators

2022 I E Block Community Lecture: AI and Cryptography
July 13, 2022 How is Artificial Intelligence (AI) changing your life and the world? How can you expect your data to be kept secure and private in an AI-driven future? Kristin Lauter of Meta AI Research gives the I. E. Block Community Lecture titled "Artificial Intelligence and Cryptograph
From playlist SIAM Conference Videos

Few other Cryptanalytic Techniques
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Overview on Modern Cryptography
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

NIST - Missions and impacts to US industry, economy and citizens - James St. Pierre, Matthew Scholl
NIST - Missions and impacts to US industry, economy and citizens - James St. Pierre, Matthew Scholl Founded in 1901 and now part of the U.S. Department of Commerce, NIST is one of the nation's oldest physical science laboratories. Congress established the agency to remove a major handicap
From playlist AppSecUSA 2013

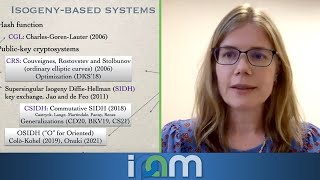
Kritin Lauter, Supersingular isogeny graphs in cryptography
VaNTAGe Seminar, September 20, 2022 License: CC-BY-NC-SA Some of the papers mentioned in this talk: Charles, Goren, Lauter 2007: https://doi.org/10.1007/s00145-007-9002-x Mackenzie 2008: https://doi.org/10.1126/science.319.5869.1481 Pizer 1990: https://doi.org/10.1090/S0273-0979-1990-15
From playlist New developments in isogeny-based cryptography

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security
Craig Costello - Post-quantum key exchange from supersingular isogenies- IPAM at UCLA
Recorded 26 July 2022. Craig Costello of Microsoft Research presents "Post-quantum key exchange from supersingular isogenies" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This talk will give an overview of Supersingular isogeny Diffie-Hellman (SIDH): t
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography
Chris Peikert - Post Quantum assumptions - IPAM at UCLA
Recorded 27 July 2022. Chris Peikert of the University of Michigan presents "Post Quantum assumptions" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Learn more online at: https://www.ipam.ucla.edu/programs/summer-schools/graduate-summer-school-on-post-quantum-and-
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Bitcoin Q&A: Migrating to Post-Quantum Cryptography
Keywords/phrases: Quantum cryptography, quantum cryptoanalysis, quantum computing. Bitcoin uses SHA-256. In cryptography there is a 20-30 year lifecycle for an algorithm before it gets exceeded by new technologies and developments in mathematics. Both the signing and hashing algorithms can
From playlist English Subtitles - aantonop Videos with subtitles in English
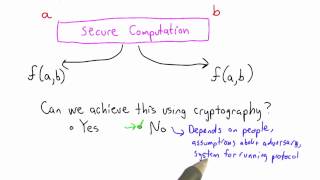
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Kirsten Eisentraeger - Classical and quantum algorithms for isogeny problems - IPAM at UCLA
Recorded 26 January 2022. Kirsten Eisentraeger of Pennsylvania State University presents "Classical and quantum algorithms for isogeny problems" at IPAM's Quantum Numerical Linear Algebra Workshop. Abstract: Isogeny-based cryptography is one of a few candidates for post-quantum cryptograph
From playlist Quantum Numerical Linear Algebra - Jan. 24 - 27, 2022

Adeline Roux-Langlois : Using structured variants in lattice-based cryptography - Lecture 1
CONFERENCE Recording during the thematic meeting : « Francophone Computer Algebra Days» the March 06, 2023 at the Centre International de Rencontres Mathématiques (Marseille, France) Filmmaker: Jean Petit Find this video and other talks given by worldwide mathematicians on CIRM's Audiov
From playlist Mathematical Aspects of Computer Science