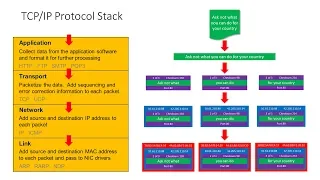
Computer Networks. Part Six: The TCP/IP Protocol Stack and Routers
This is the sixth in a series about computer networks. This video describes the role of a network protocol, and specifically details the TCP/IP suite of protocols. The need for a layered approach to networking software is discussed including the four layer TCP/IP stack and the relevance
From playlist Computer Networks

An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet

CERIAS Security: Survivable routing in wireless ad hoc networks 2/6
Clip 2/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

Communications and Network Security | CISSP Training Videos
🔥 Enroll for FREE CISSP Course & Get your Completion Certificate: https://www.simplilearn.com/learn-cloud-security-basics-skillup?utm_campaign=CCSP&utm_medium=DescriptionFirstFold&utm_source=youtube Communication and Network Security : Domain 4 of the CISSP certification course offered by
From playlist Cyber Security Playlist [2023 Updated]🔥

CERIAS Security: Survivable routing in wireless ad hoc networks 3/6
Clip 3/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

Computer Networking Course - Network Engineering [CompTIA Network+ Exam Prep]
This full college-level computer networking course will prepare you to configure, manage, and troubleshoot computer networks. It will also help you prepare for CompTIA's Network+ exam. This course was developed by Brian Ferrill, an instructor at Edmonds Community College. ⭐️ Course Conte
From playlist Networks

CERIAS Security: Survivable routing in wireless ad hoc networks 5/6
Clip 5/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

CERIAS Security: Survivable routing in wireless ad hoc networks 1/6
Clip 1/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

Speaker: Riley "Caezar" Eller, Director for Technology and Security, CoCo Communications Abstract: Mobile Ad-Hoc Networking (MANET) technology promises disaster-tolerant, interoperable, secure communications that work the way we users do. Features like automatic peer discovery and stable
From playlist DEFCON 14

CERIAS Security: Survivable routing in wireless ad hoc networks 6/6
Clip 6/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

CERIAS Security: Survivable routing in wireless ad hoc networks 4/6
Clip 4/6 Speaker: Cristina Nita-Rotaru · Purdue University In an ad hoc wireless network nodes not in direct range communicate via intermediate nodes. Thus, a significant concern is the ability to route in the presence of Byzantine failures which include nodes that drop, fabricate, mo
From playlist The CERIAS Security Seminars 2005 (1)

Lecture 2 - Types of Wireless communication
Lecture Series on Wireless Communications by Dr.Ranjan Bose, Department of Electrical Engineering, IIT Delhi. For more details on NPTEL, visit http://nptel.iitm.ac.in
From playlist Wireless Communication

CERIAS Security: Security in Infrastructureless and Decentralized Communication Networks 3/5
Clip 3/5 Speaker: Andre Koenig · Technical University Darmstadt Infrastructureless and decentralized communication substrates such as mobile ad hoc networks and peer-to-peer systems enable setting up communication services beyond borders of contemporary wired or cellular client/server sy
From playlist The CERIAS Security Seminars 2009