
Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

From playlist Week 2 2015 Shorts

Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

One Time Pad - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography
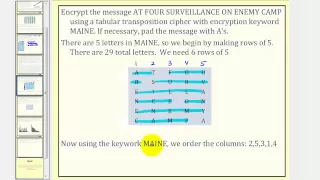
Cryptography: Transposition Cipher
This lesson explains how to encrypt and decrypt a message using a transposition cipher. Site: http://mathispower4u.com
From playlist Cryptography

This video is a brief introduction to linear codes: dimensions, G (generating matrix), H (parity check matrix), their forms. Also gives an example of how to convert between G and H. Here is the formal definition of a Linear Code: A linear code of dimension k and length n over a field
From playlist Cryptography and Coding Theory

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Math for Liberal Studies - Lecture 3.6.1 Substitution Ciphers
This is the first video lecture for Math for Liberal Studies Section 3.6: An Introduction to Cryptography. In this video, we discuss the general idea of encrypting and decrypting messages to keep unintended recipients from reading them. We then discuss some simple methods for doing this.
From playlist Math for Liberal Studies Lectures

Math for Liberal Studies - Lecture 3.7.2 The Vigenère and Autokey Ciphers
This is the second video for Math for Liberal Studies Section 3.7: Modular Arithmetic and Ciphers. In this video, we apply the modular arithmetic ideas from the previous lecture to cryptography. Specifically, we learn how to replace the letters in a message with numbers and perform "letter
From playlist Math for Liberal Studies Lectures

From playlist Week 2 2015 Shorts

caesar - CS50 Walkthroughs 2019
*** This is CS50, Harvard University's introduction to the intellectual enterprises of computer science and the art of programming. *** HOW TO SUBSCRIBE http://www.youtube.com/subscription_center?add_user=cs50tv HOW TO TAKE CS50 edX: https://cs50.edx.org/ Harvard Extension School: ht
From playlist CS50 Walkthroughs 2019

Cryptography Explained: The Science of Code
Ever seen the Da Vinci Code? You might be interested in Cryptography! There are lots of different ways to encrypt a message, from early, simple ciphers to the famous Enigma machine. Michael Aranda takes you through a fun and cryptic episode of SciShow, all about codes! ---------- SciShow h
From playlist Uploads

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Math for Liberal Studies - Lecture 3.6.2 The Bifid Cipher
This is the second video lecture for Math for Liberal Studies Section 3.6: An Introduction to Cryptography. In this lecture, we discuss a new method for encrypting and decrypting messages: the bifid cipher. This method relies on converting the letters in the message to coordinates in a let
From playlist Math for Liberal Studies Lectures


