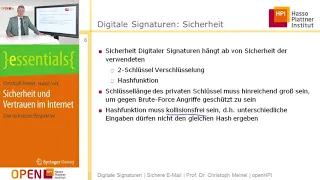
Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Signature Validation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

27c3: Die gesamte Technik ist sicher (de)
Speakers: Dominik Oepen, Frank Morgner Possession and knowledge: Relay attacks on the new ID card For the new electronic identity card three different readers classes are specified, the simplest of which has already undergone some criticism. After the discussion about the security of the
From playlist 27C3: We come in peace

#HITBLockdown D1 - 60 CVEs In 60 Days - Eran Shimony
In recent years, the most effective way to discover new vulnerabilities is considered to be fuzzing. I will present a complementary approach to fuzzing called MTE. By using MTE, I managed to get over 60 CVEs, all are logical vulnerabilities, in 60 days across many major software vendors li
From playlist Center for Applied Cybersecurity Research (CACR)

DEFCON 13: On the Current State of Remote Active OS Fingerprinting
Speaker: Ofir Arkin, CTO and Co-Founder, Insightix Active operating system fingerprinting is a technology, which uses stimulus (sends packets) in order to provoke a reaction from network elements. The implementations of active scanning will monitor the network for a response to be, or no
From playlist DEFCON 13

CERIAS Security: Automatic Signature Generation for Unknown Vulnerabilities 3/5
Clip 3/5 Speaker: Weidong Cui · Microsoft In this talk, I will present a new approach to automatically generate a vulnerability signature for an unknown vulnerability, given a zero-day attack instance. Our approach is based on two systems we developed: Tupni and ShieldGen. Tupni ta
From playlist The CERIAS Security Seminars 2008

CERIAS Security: Automatic Signature Generation for Unknown Vulnerabilities 5/5
Clip 5/5 Speaker: Weidong Cui · Microsoft In this talk, I will present a new approach to automatically generate a vulnerability signature for an unknown vulnerability, given a zero-day attack instance. Our approach is based on two systems we developed: Tupni and ShieldGen. Tupni ta
From playlist The CERIAS Security Seminars 2008

CERIAS Security: From Securing Navigation Systems to Securing Wireless Communication 2/6
Clip 2/6 Speaker: Srdjan Capkun · Assistant Professor · ETH Zurich Recent rapid development of wireless networks of sensors, actuators and identifiers dictates the digitalization of our physical world and the creation of the "internet of things". In this new internet, each wireless de
From playlist The CERIAS Security Seminars 2007
[Emc=Q] #019 - ANDREAS ANTONOPOULOS: Bitcoin Begins
THINK FINANCE IS DULL AND BORING? THINK AGAIN! CRYPTO CURRENCY TECHNOLOGY IS GONNA CONNECT THE WORLD AND SOCIALIZE MONEY THE SAME WAY THE INTERNET, FACEBOOK AND TWITTER DID WITH INFORMATION. TIME TO LET THE OTHER 6 BILLION OF THE WORLD ENJOY, CONTROL AND USE MONEY WITHOUT THE MIDDLE MEN OR
From playlist Interviews and Shows

Part II: I am Andreas Antonopoulos. Ask me hard questions about Bitcoin Part II
Want more like this? http://www.sfcryptocurrencydevs.com/ Part II of Andreas Antonopoulos Q&A with the San Francisco Bitcoin Devs meetup on May 5th, 2014
From playlist Bitcoin Talks by Andreas M. Antonopoulos

AWS IAM Tutorial | AWS Identity And Access Management | AWS Tutorial | AWS Training | Simplilearn
🔥 Cloud Architect Master's Program (Discount Code: YTBE15): https://www.simplilearn.com/cloud-solutions-architect-masters-program-training?utm_campaign=AWSIAM-3A5hRIT8zdo&utm_medium=DescriptionFF&utm_source=youtube 🔥 Caltech Cloud Computing Bootcamp (US Only): https://www.simplilearn.com/c
From playlist AWS Tutorial Videos For Beginners 🔥[2022 Updated] | Simplilearn

Network Security Tutorial | Introduction to Network Security | Network Security Tools | Edureka
🔵 Edureka Cyber Security Masters Program: https://bit.ly/3pfHHIN 🔥Edureka CompTIA Security+ Certification Training: https://bit.ly/3nxeVRl This Edureka video gives an introduction to Network Security and its nuances. Topics covered in this video are: 1.Need for Network Security 2.What is
From playlist Cyber Security Training for Beginners | Edureka

DEFCON 19: Metasploit vSploit Modules
Speakers: Marcus J. Carey Enterprise Security Community Manager, Rapid7 | David Rude AKA bannedit, @msfbannedit, Metasploit Exploit Developer | Will Vandevanter Senior Penetration Tester, Rapid7 This talk is for security practitioners who are responsible for and need to test enterprise
From playlist DEFCON 19

CERIAS Security: Automatic Signature Generation for Unknown Vulnerabilities 2/5
Clip 2/5 Speaker: Weidong Cui · Microsoft In this talk, I will present a new approach to automatically generate a vulnerability signature for an unknown vulnerability, given a zero-day attack instance. Our approach is based on two systems we developed: Tupni and ShieldGen. Tupni ta
From playlist The CERIAS Security Seminars 2008

How to Create a Gmail Signature with Logo, Image & Links
Get WiseStamp for FREE: https://bit.ly/WiseStamp_Simpletivity 🖊️ And if you need more features, upgrade with this special promo code: wisestamp-sp35 Having a great-looking email signature is essential. But if you use Gmail, what is the easiest way to create and manage your email signature
From playlist Best Gmail Tips & Tricks

Protection Of Information Assets | CISA Training Videos
Certified Information System Auditor (CISA) Protection of Information Assets Objectives: • Understand and provide assurance that the enterprise’s security policies, standards, procedures and controls ensure the confidentiality, integrity and availability of information assets • Detail the
From playlist CISA Training Videos