In this video, you’ll learn more about how hashtags are used on Twitter. Visit https://www.gcflearnfree.org/twitter/what-is-a-hashtag/1/ for our text-based lesson. This video includes information on: • Using hashtags • Browsing popular hashtags We hope you enjoy!
From playlist Twitter

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography
Cryptographic Hash Functions: Part 2
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security
Cryptographic Hash Functions: Part 1
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

Programming Ruby 07 -- Hash Ops
Operations on Hashes in Ruby -- this is an ultra-basic tutorial, designed to give you a very brief outline of how hashes work in Ruby. This is part of a "programming fundamentals" course that's designed to prepare someone for bash. http://www.ruby-doc.org/core-2.1.5/Hash.html
From playlist Programming: Ruby

Excel Hash 2021 Challenge - Secret Formula for Sales Commission
In this Excel Hash Challenge 2021, we have some great ingredients to mashup and provide solutions. This is the third edition of Excel Hash Challenge and there are some great participants around the globe. Please feel to check other participant's videos & don't forget to give a vote, like &
From playlist Excel Hash 2021

From playlist Cryptography Lectures

CERIAS Security: Recent Attacks on MD5 2/6
Clip 2/6 Speaker: John Black · University of Colorado at Boulder Cryptology is typically defined as cryptography (the construction of cryptographic algorithms) and cryptanalysis (attacks on these algorithms). Both are important, but the latter is more fun. Cryptographic hash functions
From playlist The CERIAS Security Seminars 2006

EEVblog 1494 - FIVE Ways to Open a CHEAP SAFE!
FIVE different easy methods to crack into a cheap Sandleford safe found in the dumpster, WITHOUT using physical force. Including a bonus 6th method that doesn't work on this one. Don't buy cheap hardware store safes, they are garbage! Also advice on what to look for in a good quality home
From playlist Hacking / Experiments

RubyConf 2015 - The Hitchhiker's Guide to Ruby GC by Eric Weinstein
The Hitchhiker's Guide to Ruby GC by Eric Weinstein When Ruby programs slow down, the usual culprits—database queries, superlinear time complexity—aren't always the real problem. Ruby's object space and garbage collection are a surprisingly rich and oft-misunderstood area of the language
From playlist RubyConf 2015

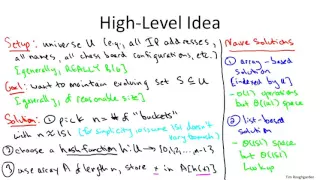
Hash Tables and Hash Functions
This computer science video describes the fundamental principles of the hash table data structure which allows for very fast insertion and retrieval of data. It covers commonly used hash algorithms for numeric and alphanumeric keys and summarises the objectives of a good hash function. Co
From playlist Data Structures

[Rust Programming] Advent of Code 2016 Day 8 - Two-Factor Authentication
My Rust solution for Day 8 of Advent of Code 2016. [NOTE: This video was streamed October 2022] I livestream these on twitch when I can, on occasional weekday mornings, starting between 7 and 7:30am Eastern/US time. I usually stream for about 1-2 hours, depending on how well my voice hol
From playlist Advent of Code 2016

MountainWest RubyConf 2014 - Big O in a Homemade Hash by Nathan Long
Rubyists use hashes all the time. But could you build Ruby's Hash class from scratch? In this talk, I'll walk you through it. We'll learn what it takes to get the interface we want and maintain O(1) performance as it grows. Help us caption & translate this video! http://amara.org/v/FG2n/
From playlist MWRC 2014

Parallelograms – Learn Basic Geometry
TabletClass Math: https://tcmathacademy.com/ Math video on parallelograms. For more math help to include math lessons, practice problems and math tutorials check out my full math help program at https://tcmathacademy.com/ Math Notes: Pre-Algebra Notes: https://tabletclass-ma
From playlist Geometry

0030 - C++ programming: Developing a Web Server from scratch
This is #30 in my series of live (Twitch) coding streams, working on writing my own web server and service framework in C++. This stream I almost finished up WebSockets. It took a bit more time than I expected. I brought in some libraries I needed: SHA-1 hash algorithm, Base64 encoder,
From playlist Excalibur

RailsConf 2022 - Keynote: RailsConf 2022 - It's been a minute! by Aaron Patterson
Keynote: RailsConf 2022 - It's been a minute! by Aaron Patterson
From playlist RailsConf 2022

RubyConf 2016 - Seeing Metaprogramming and Lambda Function Patterns in Ruby by Lukas Nimmo
RubyConf 2016 - Seeing Metaprogramming and Lambda Function Patterns in Ruby by Lukas Nimmo Metaprogramming and lambda functions in Ruby should be explained within their rightful place: living examples. You may have read tutorials on what these concepts are, but still do not understand whe
From playlist RubyConf 2016

RailsConf 2017: The Art & Craft of Secrets: Using the Cryptographic Toolbox by Michael Swieton
RailsConf 2017: The Art & Craft of Secrets: Using the Cryptographic Toolbox by Michael Swieton Picking an encryption algorithm is like choosing a lock for your door. Some are better than others - but there's more to keeping burglars out of your house (or web site) than just the door lock
From playlist RailsConf 2017