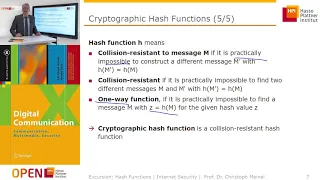
Cryptographic Hash Functions: Part 1
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography
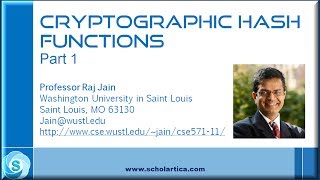
Cryptographic Hash Functions: Part 2
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

Cryptographic Hash Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

https://en.wikipedia.org/wiki/SHA-1#Examples_and_pseudocode If you have any questions of want to contribute to code or videos, feel free to write me a message on youtube or get my contact in the About section or googling my contacts.
From playlist Programming
PMSP - Quasi-random boolean functions, and inapproximability - Ryan O'Donnell
Ryan O'Donnell Carnegie Mellon University June 17, 2010 For more videos, visit http://video.ias.edu
From playlist Mathematics

From playlist Acts as Conference 2009

Hash Tables and Hash Functions
This computer science video describes the fundamental principles of the hash table data structure which allows for very fast insertion and retrieval of data. It covers commonly used hash algorithms for numeric and alphanumeric keys and summarises the objectives of a good hash function. Co
From playlist Data Structures
From playlist Cryptography Lectures

RailsConf 2015 - Building RailsPerf, a toolkit to detect performance regressions
By, Kir Shatrov Performance regressions in edge Rails versions happen quite often, and are sometimes introduced even by experienced Core commiters. The Rails team doesn’t have any tools to get notified about this kind of regressions yet. This is why I’ve built RailsPerf, a regression detec
From playlist RailsConf 2015

Blockchain was built to revolutionize how we share data...but can it live up to the promises it has built? » Subscribe to Seeker! http://bit.ly/subscribeseeker » Watch more Elements! http://bit.ly/ElementsPlaylist » Visit our shop at http://shop.seeker.com While bitcoin and blockchain a
From playlist Elements | Season 4 | Seeker

Science & Technology Q&A for Kids (and others) [Part 50]
Stephen Wolfram hosts a live and unscripted Ask Me Anything about science and technology for all ages. Find the playlist of Q&A's here: https://wolfr.am/youtube-sw-qa Originally livestreamed at: https://twitch.tv/stephen_wolfram Outline of Q&A 0:00 Stream starts 1:46 Stephen begins the s
From playlist Stephen Wolfram Ask Me Anything About Science & Technology

[Rust Programming] Learning to make a Roguelike - Day 36
[Recorded on 23 November, 2021] I've been playing Roguelikes for many years, and I've always thought about making one! Combine that with a desire to learn Rust, and we've got a match made in heaven. This session was recorded live from twitch on 23 November. I'm using the Roguelike Tutori
From playlist [Rust Programming] Writing Roguelike using RLTK

RubyConf 2021 - Parsing Ruby by Kevin Newton
Since Ruby's inception, there have been many different projects that parse Ruby code. This includes everything from development tools to Ruby implementations themselves. This talk dives into the technical details and tradeoffs of how each of these tools parses and subsequently understands
From playlist RubyConf 2021

Get the Code Here: http://goo.gl/srwIf Welcome to my Java Hash Table tutorial. A Hash Table is a data structure offers fast insertion and searching capabilities. The negative is that they are limited in size because they are based on arrays. They are also hard to order. People get confus
From playlist Java Algorithms

Hangout With CERN: Hot stuff - the early Universe (S01E06)
This Hangout takes us well into the past, as we delve into the very early Universe. The LHC can recreate these early-Universe conditions in the lab by colliding heavy ions together. But why do we collide these different particle species? What is in store for the heavy-ion collisions after
From playlist Hangouts with CERN