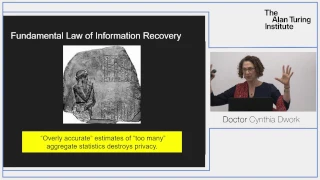
Turing Lecture: Dr Cynthia Dwork, Privacy-Preserving Data Analysis
Doctor Cynthia Dwork: Privacy-Preserving Data Analysis Privacy-preserving data analysis has a long history, spanning at least five decades and numerous disciplines. Despite this extensive history, it is only in the last decade that an understanding has formed of the risk that the accumula
From playlist Turing Lectures

Facebook: Understanding Privacy
In this video, you’ll learn more about how Facebook privacy works. Visit https://www.gcflearnfree.org/facebook101/understanding-facebook-privacy/1/ for our text-based lesson. This video includes information on: • Understanding basic privacy settings • Sharing and privacy • Facebook privac
From playlist Internet Safety

If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist The Internet

Martin Wainwright: Privacy and statistical minimax: quantitative tradeoffs
Find this video and other talks given by worldwide mathematicians on CIRM's Audiovisual Mathematics Library: http://library.cirm-math.fr. And discover all its functionalities: - Chapter markers and keywords to watch the parts of your choice in the video - Videos enriched with abstracts, b
From playlist Probability and Statistics

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course
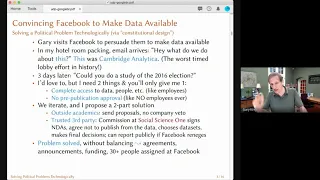
Statistically Valid Inferences from Privacy Protected Data
A Google TechTalk, presented by Gary King, 2020/09/18 Paper Title: "Statistically Valid Inferences from Privacy Protected Data" Abstract: Unprecedented quantities of data that could help social scientists understand and ameliorate the challenges of human society are presently locked away
From playlist Differential Privacy for ML
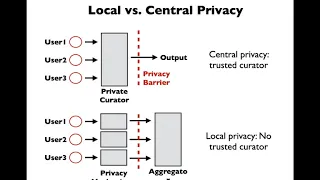
Profile-based Privacy for Locally Private Computations
A Google TechTalk, 2020/7/30, presented by Kamalika Chaudhuri, UCSD ABSTRACT: Differential privacy has emerged as a gold standard in privacy-preserving data analysis. A popular variant commonly used for federated learning is local differential privacy, where the data holder is the trusted
From playlist 2020 Google Workshop on Federated Learning and Analytics

Day 2 Lightning Talks: Privacy & Security
A Google TechTalk, Lightning Talks presented by 7 Speakers, 2021/11/9 ABSTRACT: Each talk is 7 min. plus Q&A. Track 1 - Session Chair: Peter Kairouz (Privacy & Security) 1. Andreas Haeberlen - Privacy-Preserving Federated Analytics with Billions of Users 2. Li Xiong - Federated Learning w
From playlist 2021 Google Workshop on Federated Learning and Analytics

A short tutorial on differential privacy: Dr Borja Balle, Amazon Research
Differential privacy is a robust mathematical framework for designing privacy-preserving computations on sensitive data. In this tutorial we will cover the key definitions and intuitions behind differential privacy and introduce the core building blocks used by most differentially private
From playlist Turing Seminars

Privacy-preserving algorithms for decentralised collaborative learning: Dr Aurélien Bellet
Short bio I am a tenured researcher at Inria, where I am part of the Magnet Team (MAchine learninG in information NETworks). I am also affiliated with CRIStAL (UMR CNRS 9189), a research center of the University of Lille. Prior to joining Inria, I was a postdoctoral researcher at the Uni
From playlist Turing Seminars

From PhD to PhD: A Conference Mapping the Network on Lebanese Mathematics - Day 3 - June 3, 2021
“I dislike frontiers, political or intellectual, and I find that ignoring them is an essential catalyst for creative thought. Ideas should flow without hindrance in their natural course.” Michael Atiyah In the midst of social-political turmoil, financial meltdown, disease induced lockdown,
From playlist From PhD to PhD: A Conference Mapping the Network on Lebanese Mathematics - June 1-3, 2021

Protection Of Information Assets | CISA Training Videos
Certified Information System Auditor (CISA) Protection of Information Assets Objectives: • Understand and provide assurance that the enterprise’s security policies, standards, procedures and controls ensure the confidentiality, integrity and availability of information assets • Detail the
From playlist CISA Training Videos

DSI Seminar Series | Artificial Intelligence in Support of Biomedical Data Privacy
In this Data Science Institute Seminar Series talk from July 2021, Bradley Malin, accenture professor of Biomedical Informatics, Biostatistics and Computer Science at Vanderbilt University, discusses issues surrounding biomedical data and approaches to data privacy risk assessment involvin
From playlist DSI Virtual Seminar Series

IMT4306 Mobile Research: Privacy and Anonymity
IMT4306 Introduction to Research in Mobile Decentralised systems, privacy, anonymity, privacy techniques.
From playlist 2021 - IMT4306 - Mobile Research

Google Keynote: Federated Aggregation and Privacy
A Google TechTalk, presented by Dan Ramage, Brendan McMahan, & Kallista Bonawitz, 2021/11/8 ABSTRACT: 3 Google researchers talk about the state of the art in federated aggregations and privacy. About the Speakers Brendan McMahan, Google - Brendan McMahan has worked in the fields of onlin
From playlist 2021 Google Workshop on Federated Learning and Analytics

Privacy-preserving Information Sharing: Tools and Applications: Dr Emiliano De Cristofaro
Short Bio: I am a Reader (Associate Professor) in Security and Privacy Enhancing Technologies at University College London (UCL), where I am affiliated with the Computer Science Department and the Information Security Group. Before joining UCL in 2013, I was a research scientist at Xerox
From playlist Turing Seminars

Internet Safety: Your Browser's Security Features
In this video, you’ll learn more about your browser's security features. Visit https://www.gcflearnfree.org/internetsafety/your-browsers-security-features/1/ for our text-based lesson. This video includes information on: • Using browser security to check web addresses and identify securit
From playlist Internet Tips

Pediatric Moonshot | Future of Data & AI | Data Science Dojo
Artificial Intelligence applications hold the key to reducing healthcare inequity locally and globally. While centralized architectures have been key to advances in consumer AI, they will not work to deploy and train AI applications for children’s medicine. As the pandemic shut down the wo
From playlist Future of Data and AI: Panel Discussions