
Pairwise Distribution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Secret Sharing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

From secret to WIF private key and address
In this video we discuss how to get from the secret private key number (a.k.a. exponent) to the WIF and how to get from the public key to address formats. He's the code: https://gist.github.com/Nikolaj-K/d548a12a45599070ea89ff376803758b
From playlist Programming

Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Pairwise Distribution Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Key Exchange - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Private Messages - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
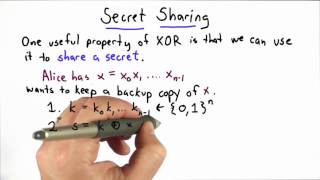
Secret Sharing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DEFCON 16: Snort Plug-in Development: Teaching an Old Pig New Tricks
Speaker: Ben Feinstein, Security Researcher, SecureWorks Counter Threat Unit Snort has become a standard component of many IT security environments. Snort is mature and widely deployed, and is no longer viewed as new or exciting by the industry. However, with such widespread deployment, e
From playlist DEFCON 16

Transformer and BERT Pre-training
In this lecture we look at the Transformer architecture for sequence contextualization, how the BERT model pre-trains Transformers, and how with the HuggingFace ecosystem the community can share models. We also overview an exemplary task for BERT: Extractive Question Answering (QA). Slide
From playlist Advanced Information Retrieval 2021 - TU Wien

Keynote Presentation: Brian Nosek
Brian Nosek discusses the Open Science Framework, its use and adoption as a platform for open data and open science.
From playlist Yale Day of Data 2016

Modular and Composable Transfer Learning with Jonas Pfeiffer
Research Scientist Jonas Pfeiffer (Google Research) presents on modular and composable transfer learning. What you can look forward to learning from Jonas: "With pre-trained transformer-based models continuously increasing in size, there is a dire need for parameter-efficient and modular
From playlist Tango

Importance Of Keys Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

What Lies Beneath - A Deep Dive Into Clojure's Data Structures - Mohit Thatte
Immutable, persistent data structures are at the heart of Clojure's philosophy. It is instructive to see how these are implemented, to appreciate the trade-offs between persistence and performance. Lets explore the key ideas that led to effective, practical implementations of these data st
From playlist Clojure, Lisp

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

IMT4889: Evaluation of messaging protocols
IMT4889 - Specialisation in Decentralised Technologies Evaluation of messaging protocols
From playlist 2021 - IMT4889 - Decentralisation

Chuck Eesley discusses venture financing and raising money. In this video, pre and post-money valuation along with dilution are discussed with example calculations. Take the quizzes and find the rest of the course at http://eesley.blogspot.com Stanford University: http://www.stanford.edu
From playlist Lecture Collection | Technology Entrepreneurship

Storing Passwords Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DeBERTa: Decoding-enhanced BERT with Disentangled Attention (Machine Learning Paper Explained)
#deberta #bert #huggingface DeBERTa by Microsoft is the next iteration of BERT-style Self-Attention Transformer models, surpassing RoBERTa in State-of-the-art in multiple NLP tasks. DeBERTa brings two key improvements: First, they treat content and position information separately in a new
From playlist Papers Explained
