
Permutations and Combinations Tutorial
This video tutorial focuses on permutations and combinations. It contains a few word problems including one associated with the fundamental counting principle. Permutations are useful to determine the different number of ways to arrange something where as combinations is useful for deter
From playlist Pre-Algebra Video Playlist
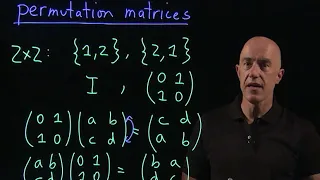
Permutation matrices | Lecture 9 | Matrix Algebra for Engineers
What is a permutation matrix? Define 2x2 and 3x3 permutation matrices. Join me on Coursera: https://www.coursera.org/learn/matrix-algebra-engineers Lecture notes at http://www.math.ust.hk/~machas/matrix-algebra-for-engineers.pdf Subscribe to my channel: http://www.youtube.com/user/jch
From playlist Matrix Algebra for Engineers

Modifying a Perforce Workspace
This video covers how to modify an existing Perforce workspace using P4V. Additional videos in this series: Lesson01: Getting Started with Perforce and P4V (https://youtu.be/Yvgxx2vwsRY) Lesson02: Basic Operations with Perforce (https://youtu.be/_5_LK_0H22I) Lesson03: Modifying a Perforce
From playlist Working with Perforce and P4V

Adding and Deleting Users on a Perforce Server
In this video we show how to add and delete users from a Perforce server. Additional videos in this series: -Getting Started with Perforce and P4V (https://youtu.be/Yvgxx2vwsRY) -Basic Operations with Perforce (https://youtu.be/_5_LK_0H22I) -Modifying a Perforce Workspace (https://youtu.b
From playlist Working with Perforce and P4V

Basic Operations with Perforce
This video covers how to perform basic operations with Perforce using the P4V interface. This includes creating a changelist, checking out files, modifying files, and submitted changes back to the server. Additional videos in this series: -Getting Started with Perforce and P4V (https://y
From playlist Working with Perforce and P4V
Evaluate Factorials, Permulations, and Combinations Using a Free Online Tool (MOER/Mathas)
This video shows how to evaluate factorials, permutations, and combinations using a free online tool. https://oervm.s3-us-west-2.amazonaws.com/tvm/indexCP.html
From playlist Probability

PERL Tutorial - 2 | PERL Tutorial for Beginners - 2 | Learn PERL | Mastering Perl Scripting
( https://www.edureka.co/mastering-perl-scripting-self-paced ) Perl is one of the most popular open source interpreted programming languages with a huge number of programmers, libraries and resources. Programmers are using Perl from decades because of its extensive libraries, consistently
From playlist Perl Scripting Tutorial Videos

Secure computation with RAMs - Dr Mariana Raykova, Yale University
Secure computation with RAMs: revisiting square root ORAM and low leakage secure Boolean queries Hiding memory access patterns is required for secure computation, but remains prohibitively expensive for many interesting applications. This talk presents two works addressing this question:
From playlist Turing Seminars

L23.3 Permutation operators on N particles and transpositions
MIT 8.06 Quantum Physics III, Spring 2018 Instructor: Barton Zwiebach View the complete course: https://ocw.mit.edu/8-06S18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP60Zcz8LnCDFI8RPqRhJbb4L L23.3 Permutation operators on N particles and transpositions License: Cr
From playlist MIT 8.06 Quantum Physics III, Spring 2018

This project was created with Explain Everything™ Interactive Whiteboard for iPad.
From playlist Modern Algebra - Chapter 16 (permutations)

Introduction to combinations | Probability and Statistics | Khan Academy
Watch the next lesson: https://www.khanacademy.org/math/probability/probability-and-combinatorics-topic/combinations-combinatorics/e/combinations_1?utm_source=YT&utm_medium=Desc&utm_campaign=ProbabilityandStatistics Watch the next lesson: https://www.khanacademy.org/math/probability/proba
From playlist High school statistics | High School Math | Khan Academy

Flipped learning with Jupyter: Experiences, best practices, and supporting research
Flipped learning with Jupyter: Experiences, best practices, and supporting research Lorena Barba (George Washington University), Robert Talbert (Grand Valley State University) Jupyter has exploded in popularity, in not only data science but also education. As seen in the Gallery of Intere
From playlist JupyterCon in New York 2018

Stanford Seminar - Dataflow for convergence of AI and HPC - GroqChip!
Dennis Abts, Groq Oskar Mencer, Maxeler/Groq May 18, 2022 This talk provides a journey through Dataflow history, arriving at the recent convergence of AI and HPC, with the novel Groq architecture, the tensor streaming processor (TSP), combining elements from traditional dataflow architect
From playlist Stanford EE380-Colloquium on Computer Systems - Seminar Series

How many ways can you arrange the letters of “Christmas” ?
How to solve a counting problem using permutations. For more in-depth math help check out my catalog of courses. Every course includes over 275 videos of easy to follow and understand math instruction, with fully explained practice problems and printable worksheets, review notes and qu
From playlist GED Prep Videos

Representation Theory(Repn Th) 3 by Gerhard Hiss
DATE & TIME 05 November 2016 to 14 November 2016 VENUE Ramanujan Lecture Hall, ICTS Bangalore Computational techniques are of great help in dealing with substantial, otherwise intractable examples, possibly leading to further structural insights and the detection of patterns in many abstra
From playlist Group Theory and Computational Methods

Hamiltonicity of Cayley graphs and Gray codes: open problems by Elena Konastantinova
DATE & TIME 05 November 2016 to 14 November 2016 VENUE Ramanujan Lecture Hall, ICTS Bangalore Computational techniques are of great help in dealing with substantial, otherwise intractable examples, possibly leading to further structural insights and the detection of patterns in many abstra
From playlist Group Theory and Computational Methods

Operators in PERL | Learn PERL | PERL Tutorial for Beginners | Edureka
( https://www.edureka.co/mastering-perl-scripting-self-paced ) Perl is one of the most popular open source interpreted programming languages with a huge number of programmers, libraries and resources. Programmers are using Perl from decades because of its extensive libraries, consistently
From playlist Perl Scripting Tutorial Videos


