
Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Stanford Seminar - Cryptology and Security: the view from 2016 - Whitfield Diffie
"Cryptology and Security: the view from 2016" - Whitfield Diffie, ACM 2015 Turing Award About the talk: On the face of it, the cryptographers have solved their piece of the puzzle but every other aspect of security, from crypto-implementations to operating systems to applications, stinks.
From playlist Engineering

Private Messages Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Stanford Seminar - How Not to Generate Random Numbers
"How not to generate random numbers" - Nadia Heninger of University of Pennsylvania Colloquium on Computer Systems Seminar Series (EE380) presents the current research in design, implementation, analysis, and use of computer systems. Topics range from integrated circuits to operating syst
From playlist Engineering

Network Security, Part 2 : Public Key Encryption
Fundamental concepts of public key encryption are discussed. RSA encryption method explained with an example. Confidentiality of message is presented.
From playlist Cryptography, Security

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security
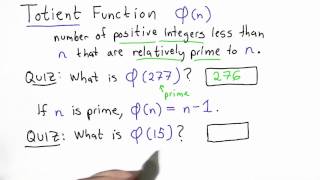
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Few other Cryptanalytic Techniques
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live

Stanford Seminar - The Evolution of Public Key Cryptography
EE380: Computer Systems Colloquium Seminar The Evolution of Public Key Cryptography Speaker: Martin Hellman, Stanford EE (Emeritus) While public key cryptography is seen as revolutionary, after this talk you might wonder why it took Whit Diffie, Ralph Merkle and Hellman so long to discov
From playlist Stanford EE380-Colloquium on Computer Systems - Seminar Series

SHA: Secure Hashing Algorithm - Computerphile
Secure Hashing Algorithm (SHA1) explained. Dr Mike Pound explains how files are used to generate seemingly random hash strings. EXTRA BITS: https://youtu.be/f8ZP_1K2Y-U Tom Scott on Hash Algorithms: https://youtu.be/b4b8ktEV4Bg http://www.facebook.com/computerphile https://twitter.com/
From playlist Cryptography on Numberphile and Computerphile

The True Story of the Windows _NSAKEY
Microsoft _NSAKEY is a signing key found in Microsoft's CryptoAPI since Windows 95. Many claimed this was the ultimate backdoor for the National Security Agency. But is this a hoax, or is the _NSAKEY a real backdoor in Microsoft Windows? A British researcher discovered that Microsoft was
From playlist Decrypted Lies

SHA 256 | SHA 256 Algorithm Explanation | How SHA 256 Algorithm Works | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=SHA256&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_campai
From playlist Big Data Hadoop Tutorial Videos For Beginners [2022 Updated]

DEFCON 20: Bruce Schneier Answers Your Questions
Speaker: BRUCE SCHNEIER Bruce Schneier will answer questions topics ranging from the SHA-3 competition to the TSA to trust and society to squid. Internationally renowned security technologist Bruce Schneier has authored twelve books -- most recently Liars and Outliers -- and hundreds of
From playlist DEFCON 20

Overview - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
