
Few other Cryptanalytic Techniques
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
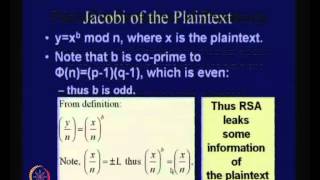
Some Comments on the Security of RSA
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
Stanford Seminar - Cryptology and Security: the view from 2016 - Whitfield Diffie
"Cryptology and Security: the view from 2016" - Whitfield Diffie, ACM 2015 Turing Award About the talk: On the face of it, the cryptographers have solved their piece of the puzzle but every other aspect of security, from crypto-implementations to operating systems to applications, stinks.
From playlist Engineering

Network Security, Part 2 : Public Key Encryption
Fundamental concepts of public key encryption are discussed. RSA encryption method explained with an example. Confidentiality of message is presented.
From playlist Cryptography, Security

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography
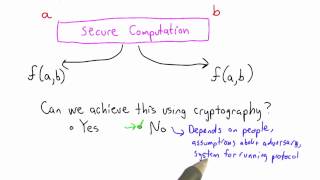
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security

Stanford Seminar - How Not to Generate Random Numbers
"How not to generate random numbers" - Nadia Heninger of University of Pennsylvania Colloquium on Computer Systems Seminar Series (EE380) presents the current research in design, implementation, analysis, and use of computer systems. Topics range from integrated circuits to operating syst
From playlist Engineering

Stanford Seminar - The Evolution of Public Key Cryptography
EE380: Computer Systems Colloquium Seminar The Evolution of Public Key Cryptography Speaker: Martin Hellman, Stanford EE (Emeritus) While public key cryptography is seen as revolutionary, after this talk you might wonder why it took Whit Diffie, Ralph Merkle and Hellman so long to discov
From playlist Stanford EE380-Colloquium on Computer Systems - Seminar Series

RSA Conference 2010 USA: The Cryptographers Panel 5/6
Clip 5/6 MODERATOR: Ari Juels, Chief Scientist and Director, RSA Laboratories PANELISTS: Whitfield Diffie, Martin Hellman, Ronald Rivest, Adi Shamir, Brian Snow Join the founders of the field for an engaging discussion about the latest advances in cryptography, research areas to wa
From playlist RSA Conference USA 2010

For more information and to download the video visit: http://bit.ly/30C3_info Playlist 30C3: http://bit.ly/30c3_pl Speakers: Nadia Heninger | djb | Tanja Lange This was a busy year for crypto. TLS was broken. And then broken again. Discrete logs were computed. And then computed again.
From playlist 30C3

Software developer explains Open Source as a business
In today's talk with David from Safing.io we are discussing Open Source software development as a business model and why opening source code is important and even beneficial for a business and a society. Follow David and Safing safing.io stamp.community twitter.com/davegson Timestamps
From playlist Cyber politics

Discovery of Public Key Cryptography with Whitfield Diffie (2015 Turing Award)
2015 Turing Award recipient Whitfield Diffie tells the story of how he discovered public key cryptography and the Diffie-Hellman key exchange. Whit was first introduced to cryptography at school, but didn’t return to it until after the completion of his degree at MIT, when he was working
From playlist Interviews

ShmooCon 2014: Keynote - Privacy Online: What Now?
For more information visit: http://bit.ly/shmooc14 To download the video visit: http://bit.ly/shmooc14_down Playlist Shmoocon 2014: http://bit.ly/shmooc14_pl Speaker: Ian Goldberg Recent revelations about data and metadata collection of Internet users' communications have been extremely
From playlist ShmooCon 2014

Stanford Seminar - Building a Trustworthy Business in the Post-Snowden Era
"Building a Trustworthy Business in the Post-Snowden Era" -Alex Stamos, Artemis Internet Colloquium on Computer Systems Seminar Series (EE380) presents the current research in design, implementation, analysis, and use of computer systems. Topics range from integrated circuits to operatin
From playlist Engineering
Do Not Implement Your Own Crypto Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Martin Hellman: The Wisdom of Foolishness
Stanford Engineering Hero Lecture When Martin Hellman started working in cryptography in the early 1970s, his colleagues told him he was crazy to do so; he couldn't possibly compete with the U.S. National Security Agency (NSA) and its enormous budget. He was also warned that if he did acco
From playlist Stanford Engineering Hero Lectures
