
Microsoft Edge: Privacy and Security in Edge
In this video, you’ll learn more about privacy and security in Edge. Visit https://www.gcflearnfree.org/edge/privacy-and-security-in-edge/1/ for our text-based lesson. This video includes information on: • Maintaining privacy in Edge • Clearing browsing history and data • Creating a priva
From playlist Microsoft Edge

Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security

Microsoft Edge: Customizing Edge
In this video, you’ll learn more about customizing Edge. Visit https://www.gcflearnfree.org/edge/customizing-edge/1/ for our text-based lesson. This video includes information on: • Choosing a homepage • Setting Edge as the default browser • Installing and removing extensions We hope you
From playlist Microsoft Edge

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
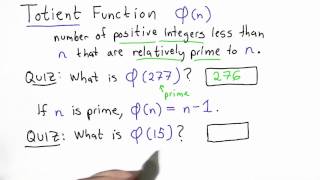
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

24C3: Why Silicon-Based Security is still that hard: Deconstructing Xbox 360 Security
Speakers: Michael Steil, Felix Domke Console Hacking 2007 The Xbox 360 probably is the video game console with the most sophisticated security system to date. Nevertheless, is has been hacked, and now Linux can be run on it. This presentation consists of two parts. In the first par
From playlist 24C3: Full steam ahead

DeepSec 2011: Why the software we use is designed to violate our privacy
Speaker: Christopher Soghoian Through the adoption of Web 2.0 and cloud based services, we have increasingly come to rely upon free services provided by commercial entities. Web mail, online backup, social networking, photo sharing, web browsers, pdf readers, anti virus software, etc. So
From playlist DeepSec 2011

The True Story of the Windows _NSAKEY
Microsoft _NSAKEY is a signing key found in Microsoft's CryptoAPI since Windows 95. Many claimed this was the ultimate backdoor for the National Security Agency. But is this a hoax, or is the _NSAKEY a real backdoor in Microsoft Windows? A British researcher discovered that Microsoft was
From playlist Decrypted Lies

22C3: "Xbox" and "Xbox 360" Hacking
Speakers: Felix Domke, Michael Steil 17 Mistakes Microsoft Made in the Xbox Security System & Xbox 360 Hacking A lot about Xbox hacking has been published earlier. This talk summarizes all this, explains some very cool new hacks and analyzes the 15 mistakes Microsoft made in the Xbox sec
From playlist 22C3: Private Investigations

Countermeasures - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DEFCON 18: Your ISP and the Government: Best Friends Forever 2/3
Speaker: Christopher Soghoian Your Internet, phone and web application providers are all, for the most part, in bed with the government. They all routinely disclose their customers' communications and other private data to law enforcement and intelligence agencies. Worse, firms like
From playlist DEFCON 18-1

Azure Import Export Service | Azure Tutorial for Beginners | Microsoft Azure Training | Edureka
🔥 Edureka Microsoft Azure Certification training (𝐔𝐬𝐞 𝐂𝐨𝐝𝐞: 𝐘𝐎𝐔𝐓𝐔𝐁𝐄𝟐𝟎) : https://www.edureka.co/microsoft-azure-administrator-certification-training This Edureka video on '𝐀𝐳𝐮𝐫𝐞 𝐈𝐦𝐩𝐨𝐫𝐭 𝐄𝐱𝐩𝐨𝐫𝐭 𝐒𝐞𝐫𝐯𝐢𝐜𝐞' will give you an overview of Import/Export Services in Microsoft Azure and will help you
From playlist Microsoft Azure Training Videos

Cyber Security Week Day - 4 | Cyber Security Interview Questions And Answers 2021 | Simplilearn
🔥Free Cyber Security Course: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CSWEEKNOV5&utm_medium=DescriptionFirstFold&utm_source=youtube This Simplilearn video on Cyber Security Interview Questions And Answers acquaints you with the top cyber security intervi
From playlist Simplilearn Live

Basics Of Cybersecurity For Beginners | Cybersecurity Fundamentals | Cybersecurity | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=BasicsOfCybersecurityForBeginners&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cy
From playlist Cyber Security Playlist [2023 Updated]🔥

How To Become Azure Administrator Associate | Session 10 | #programming
Don’t forget to subscribe! In this project, you learn how to become an Azure administrator associate. In this tutorial, we will fully cover Exam AZ-100: Microsoft Azure Infrastructure and Deployment and Exam AZ-101: Microsoft Azure Integration and Security which are the first part of g
From playlist Become Azure Administrator Associate

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security

DEFCON 20: Hacking Measured Boot and UEFI
Speakers: DAN GRIFFIN PRESIDENT, JW SECURE, INC. There's been a lot buzz about UEFI Secure Booting, and the ability of hardware and software manufacturers to lock out third-party loaders (and rootkits). Even the NSA has been advocating the adoption of measured boot and hardware-based int
From playlist DEFCON 20
