Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security
Fundamental concepts of IPSec are discussed. Authentication Header is explained. Encapsulating Security Payload (ESP) and Internet Key Exchange (IKE) are analyzed.
From playlist Network Security
Block Ciphers and Data Encryption Standard (DES): Part 2
Fundamental concepts of Block Cipher Design Principles are discussed. Differential cryptanalysis and linear cryptanalysis are explained.
From playlist Network Security

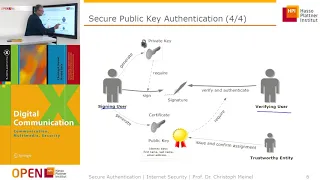
Network Security, Part 2 : Public Key Encryption
Fundamental concepts of public key encryption are discussed. RSA encryption method explained with an example. Confidentiality of message is presented.
From playlist Cryptography, Security

Symmetric Key Cryptography | Stream Cipher & Block Cipher Explained | Network Security | Simplilearn
This video on Symmetric Key Cryptography will acquaint you with the process of symmetric encryption and decryption. Here, we take a small recap into cryptography, the working and applications of symmetric key cryptography, and its advantages. We also have stream cipher and block cipher exp
From playlist Cyber Security Playlist [2023 Updated]🔥
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security

22C3: COMPLETE Hard Disk Encryption with FreeBSD
Speaker: Marc Schiesser Learn how to effectively protect not only your data but also your applications Most technologies and techniques intended for securing digital data focus on protection while the machine is turned on -- mostly by defending against remote attacks. An attacker with ph
From playlist 22C3: Private Investigations

ESXiArgs Ransomware Analysis with @fwosar
Join us as we reverse engineer the ESXiArgs ransomware used in wide spread attacks targeting unpatched VMware servers with CVE-2021-21974. Fabian (https://twitter.com/fwosar) joins us to do the heavy lifting! Tutorial that may assist with decrypting files that have been encrypted by E
From playlist Open Analysis Live!

#382 Secure and cool Remote Controls (Touchless, AES128 encryption, with a T-Beam watch and a cat)
Using remote controls to switch something on or open your garage is a piece of cake. Doing this automatically without touching anything is a little bit cooler. And doing it like James Bond, with an ESP32 Watch and completely encrypted? Let’s have a closer look at how this can be done and h
From playlist ESP32

The Complete VeraCrypt Encryption Tutorial
Hey guys! HackerSploit here back again with another video, in this video, I will be showing you how to use VeraCrypt to create encrypted volumes and how to encrypt drives. Links Used In Video: https://veracrypt.ft/en/ Our Platforms: Hsploit: https://hsploit.com/ HackerSploit Forum: https
From playlist Ethical Hacking & Penetration Testing - Complete Course

The Art and Science of Secret Messages: Some Glimpses (ONLINE) by Geetha Venkataraman
KAAPI WITH KURIOSITY THE ART AND SCIENCE OF SECRET MESSAGES: SOME GLIMPSES (ONLINE) SPEAKER: Geetha Venkataraman (Dr. B. R. Ambedkar University Delhi, Delhi) WHEN: 4:00 pm to 5:30 pm Sunday, 19 September 2021 WHERE: Livestream via the ICTS YouTube channel Abstract:- In the modern worl
From playlist Kaapi With Kuriosity (A Monthly Public Lecture Series)

Blackmatter Ransomware - Livestream Lunch and Learn: Reverse Engineering and Binary Attribution
Join us for a look into Blackmatter Ransomware. We will examine how it operates, and how it was attributed to the developers of Darkside Ransomware. Expand for more... ----- OALABS DISCORD https://discord.gg/6h5Bh5AMDU OALABS PATREON https://www.patreon.com/oalabs OALABS GITHUB https:/
From playlist Open Analysis Live!
Lecture - 33 Basic Cryptographic Concepts Part : II
Lecture Series on Internet Technologies by Prof.I.Sengupta, Department of Computer Science & Engineering ,IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Cryptography, Security

The Complete PGP Encryption Tutorial | Gpg4win & GnuPG
Hey guys! HackerSploit here back again with another video, in this video, I will be showing you how to use PGP on Windows and Linux with Gpg4win and GnuPG. Links Used In Video: gpg4win: https://www.gpg4win.org HACKERSPLOIT WEBSITE: https://hsploit.com/ ⭐SUPPORT HACKERSPLOIT BY USING THE
From playlist Ethical Hacking & Penetration Testing - Complete Course

Shell Scripting - File Encrypter/Decrypter
Hey guys! HackerSploit here back again with another video, in this series we will be looking at how to create shell scripts. A shell script is a computer program designed to be run by the Unix shell, a command-line interpreter. The various dialects of shell scripts are considered to be scr
From playlist Shell Scripting

Cyber Security Questions & Answers - Interactive Quiz | Cyber Security Training | 2022 | Simplilearn
🔥Explore Our Free Courses With Completion Certificate by SkillUp: https://www.simplilearn.com/skillup-free-online-courses?utm_campaign=QuizLiveApr28&utm_medium=Description&utm_source=youtube This YouTube live quiz on cybersecurity will be touching upon the basics of information security an
From playlist Quiz Contests | Simplilearn