From playlist Linear Transformations

Introduction to Absolute Value (2 of 2: Basic Examples)
More resources available at www.misterwootube.com
From playlist Working with Functions

Critical Values of Functions (2 of 2: Odd and Even Correspondence in derivatives and primitives)
More resources available at www.misterwootube.com
From playlist Further Work with Functions (related content)

It’s all too easy to be extremely tough on ourselves; we need – at points – to get better at self-compassion. Here is an exercise in how to lessen the voices of self-flagellation. If you like our films, take a look at our shop (we ship worldwide): https://goo.gl/dJJMFS FURTHER READING
From playlist SELF

More resources available at www.misterwootube.com
From playlist Logarithms and Exponentials

Absolute Value Equations & Inequalities (4 of 4: Graphing to avoid unnecessary algebra)
More resources available at www.misterwootube.com
From playlist Working with Functions

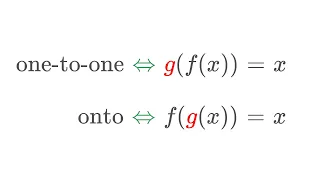
Proof: Two-Sided Inverse Functions are Unique
An explanation of why a function has at most one two-sided inverse. To prove this result, we prove that an injective function has at most one right inverse. Functions playlist: https://youtube.com/playlist?list=PLug5ZIRrShJG35bSmijiKFxerMar8jMCi Subscribe to see more new math videos! Mu
From playlist Functions

Black Hat USA 2010: Advanced AIX Heap Exploitation Methods 2/5
Speaker: Tim Shelton With the ever increasing importance of providing and maintaining reliable services for both infrastructure support as well as business continuity, companies rely upon the IBM AIX operating system. In most cases, these machines hold the most critical data available for
From playlist Black Hat USA 2010

Hackenbush Part 2: Infinitesimals
In this video, we continue our exploration of Hackenbush and learn more about winning strategies and theories.
From playlist Intro to Some Partizan Combinatorial Games and Their Theory
Jim Nolen: "A free boundary problem from Brownian bees in the infinite swarm limit in R^d"
High Dimensional Hamilton-Jacobi PDEs 2020 Workshop IV: Stochastic Analysis Related to Hamilton-Jacobi PDEs "A free boundary problem from Brownian bees in the infinite swarm limit in R^d" Jim Nolen - Duke University Abstract: I will discuss a stochastic interacting particle system in R^d
From playlist High Dimensional Hamilton-Jacobi PDEs 2020

Guy Rothblum - Group Fairness and Individual Fairness Pt. 2/2 - IPAM at UCLA
Recorded 11 July 2022. Guy Rothblum of Apple Inc. presents "Group Fairness and Individual Fairness" at IPAM's Graduate Summer School on Algorithmic Fairness. Abstract: The early literature on the theory of algorithmic fairness identified two categories of fairness notions: group fairness,
From playlist 2022 Graduate Summer School on Algorithmic Fairness

Live CEOing Ep 342: Combinators in Wolfram Language and Wolfram Physics
In this episode of Live CEOing, Stephen Wolfram discusses the language design of Wolfram Language functions relating to combinators and the Wolfram Physics Project. If you'd like to contribute to the discussion in future episodes, you can participate through this YouTube channel or through
From playlist Behind the Scenes in Real-Life Software Design

Black Hat USA 2010: Advanced AIX Heap Exploitation Methods 3/5
Speaker: Tim Shelton With the ever increasing importance of providing and maintaining reliable services for both infrastructure support as well as business continuity, companies rely upon the IBM AIX operating system. In most cases, these machines hold the most critical data available for
From playlist Black Hat USA 2010

MIT 6.046J Design and Analysis of Algorithms, Spring 2015 View the complete course: http://ocw.mit.edu/6-046JS15 Instructor: Amartya Shankha Biswas In this recitation, problems related to 2-3 Trees and B-Trees are discussed. License: Creative Commons BY-NC-SA More information at http://o
From playlist MIT 6.046J Design and Analysis of Algorithms, Spring 2015

MIT 6.172 Performance Engineering of Software Systems, Fall 2018 Instructor: Julian Shun View the complete course: https://ocw.mit.edu/6-172F18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP63VIBQVWguXxZZi0566y7Wf Prof. Shun discusses an array of bit hacks and discuss
From playlist MIT 6.172 Performance Engineering of Software Systems, Fall 2018

[Discrete Mathematics] Tree Directories and Traversals
We look at tree directories and tree traversals. Post order traversal, in order traversal, and pre order traversal. Visit our website: http://bit.ly/1zBPlvm Subscribe on YouTube: http://bit.ly/1vWiRxW *--Playlists--* Discrete Mathematics 1: https://www.youtube.com/playlist?list=PLDDGPdw7
From playlist Discrete Math 2

Functions with a Two-Sided Inverse are Bijective
One way to prove that a function is bijective is to find a two-sided inverse function. In this video, we explain why having a two-sided inverse means that a function is a bijection! Subscribe to see more new math videos! Music: OcularNebula - The Lopez
From playlist Functions
Before we carry on with our coset journey, we need to discover when the left- and right cosets are equal to each other. The obvious situation is when our group is Abelian. The other situation is when the subgroup is a normal subgroup. In this video I show you what a normal subgroup is a
From playlist Abstract algebra
What is Morality? - https://aperture.gg/morality Learn everything STEM related today with Brilliant!: https://brilliant.org/aperture Merch: https://aperture.gg/merch Talking about morality in a sense, makes us all more moral. Because it teaches us why we are the way we are, and how we can
From playlist Philosophy & Psychology 🧠

Stanford Lecture: Donald Knuth - "Trees, Rivers, and RNA" (2006)
Don Knuth's 12th Annual Christmas Tree Lecture December 6, 2006 Professor Knuth is the Professor Emeritus at Stanford University. Dr. Knuth's classic programming texts include his seminal work The Art of Computer Programming, Volumes 1-3, widely considered to be among the best scientific
From playlist Donald Knuth Lectures