
Hibernate Tutorial 01 - Introduction To Hibernate
In this tutorial, we'll understand the mismatch between object and relational models and what ORM is.
From playlist Hibernate

Hibernate Tutorial 21 - CRUD Operations
Writing code to Create, Read, Update and Delete entities in the database.
From playlist Hibernate
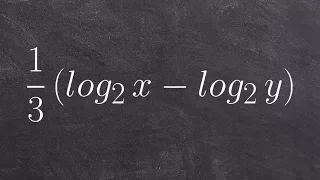
How to condense a logarithmic expression using a radical
👉 Learn how to condense logarithmic expressions. A logarithmic expression is an expression having logarithms in it. To condense logarithmic expressions means to use the logarithm laws to reduce logarithm expressions from the expanded form to a condensed form. Knowledge of the logarithm law
From playlist Condense Logarithms with Brackets

Hibernate - The Ultimate ORM Framework | Edureka
Watch Sample Class recording: http://www.edureka.co/persistence-with-hibernate?utm_source=youtube&utm_medium=webinar&utm_campaign=hibernate-webinar-23-12-14 Hibernate ORM (Hibernate in short) is an object-relational mapping library for the Java language, providing a framework for mapping
From playlist Webinars by Edureka!

Hibernate Tutorial 03 Part 1- Writing a Hibernate Application
In this first of a three part video on writing a simple Hibernate application from the scratch, we'll learn how to write the Hibernate configuration XML file, hibernate.cfg.xml.
From playlist Hibernate

Hibernate Tutorial 28 - Named Queries
We'll learn about named queries and how to write and access named queries. We'll also write and execute a NamedNativeQuery.
From playlist Hibernate
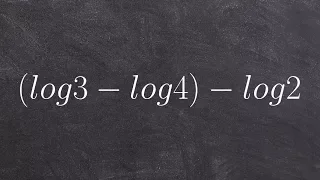
Condensing a logarithmic expression and simplifying the expression
👉 Learn how to condense logarithmic expressions. A logarithmic expression is an expression having logarithms in it. To condense logarithmic expressions means to use the logarithm laws to reduce logarithm expressions from the expanded form to a condensed form. Knowledge of the logarithm law
From playlist Condense Logarithms with Brackets
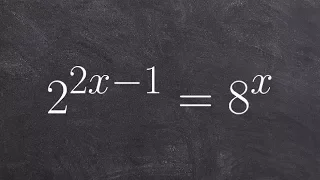
What is exponential and logarithmic form
👉 Learn how to convert an exponential equation to a logarithmic equation. This is very important to learn because it not only helps us explain the definition of a logarithm but how it is related to the exponential function. Knowing how to convert between the different forms will help us i
From playlist Logarithmic and Exponential Form | Learn About

Using the inverse of an exponential equation to find the logarithm
👉 Learn how to convert an exponential equation to a logarithmic equation. This is very important to learn because it not only helps us explain the definition of a logarithm but how it is related to the exponential function. Knowing how to convert between the different forms will help us i
From playlist Logarithmic and Exponential Form | Learn About

Hibernate Tutorial 29 - Introduction to Criteria API
This tutorial is an introduction to the Criteria API. Yet another way to work with data in Hibernate.
From playlist Hibernate