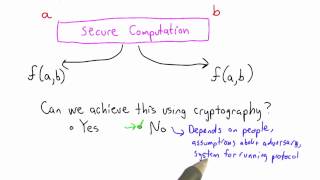
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptographic Hash Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

11/14/2019, Erich Kaltofen, North Carolina State University
Erich Kaltofen, North Carolina State University Title: Proof-of-work Certificates for High Complexity Computations for Linear Algebra Abstract: Computations done by high-power cloud servers such as a Google data center can yield outputs that are easy to verify, such as the factors of an
From playlist Fall 2019 Symbolic-Numeric Computing Seminar
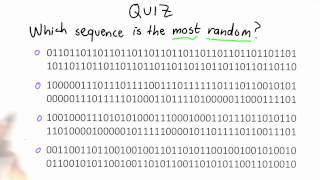
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Introduction - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
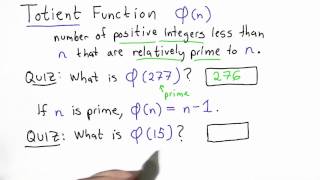
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
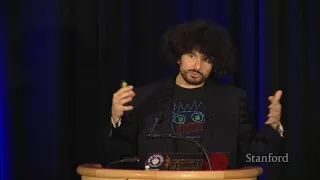
Stanford Seminar - Doubly-efficient zkSNARKs Without Trusted Setup
zkSNARKs: what are they? How do their principles apply to security? And more importantly, what is their relationship to cryptocurrency? Join Riad Wahby as he presents his team’s work on Zero-Knowledge Succinct Non-Interactive Argument of Knowledge, also known as zkSNARKs. This presentat
From playlist Stanford Seminars

Lilya Budaghyan : On APN and AB power functions
CONFERENCE Recording during the thematic meeting : « ALgebraic and combinatorial methods for COding and CRYPTography» the February 23, 2023 at the Centre International de Rencontres Mathématiques (Marseille, France) Filmmaker: Guillaume Hennenfent Find this video and other talks given b
From playlist Combinatorics

Where Did Bitcoin Come From? – The True Story
Join my Discord Community today - https://discord.gg/coldfusion - Thanks to Discord for sponsoring today’s video. Episode 2 of the Bitcoin story: https://youtu.be/iYn6EQDqTkU --- About ColdFusion --- ColdFusion is an Australian based online media company independently run by Dagogo Altra
From playlist Blockchain and Crypto
PMSP - Computational pseudo-randomness and extractors I - Russell Impagliazzo
Russell Impagliazzo UC San Diego and Institute for Advanced Study June 14, 2010 For more videos, visit http://video.ias.edu
From playlist Mathematics

23C3: Building an Open Source PKI using OpenXPKI
Speakers: Alexander Klink,Michael Bell Take a lot of Perl, add some OpenSSL, sprinkle it with a few HSMs, stir, season to taste, enjoy! OpenXPKI is an open source trust center software, written by the OpenXPKI Project, which aims to create an enterprise-scale PKI solution. You can see
From playlist 23C3: Who can you trust

In this session, Cory discusses the tools for using cryptography in Swift, and introduces a new Apple open source project for working with cryptography on all platforms, Swift Crypto. PUBLICATION PERMISSIONS: Original video was published with the Creative Commons Attribution license (reus
From playlist Blockchain

25c3: eVoting after Nedap and Digital Pen
Speaker: Ulrich Wiesner Why cryptography might not fix the issue of transparent elections Cryptographic methods have been suggested as a solution of the transparency and auditability issues in electronic voting. This talk introduces some of the suggested approaches and explains why such
From playlist 25C3: Nothing to hide

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

