
Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
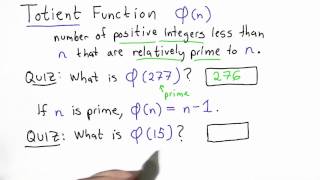
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
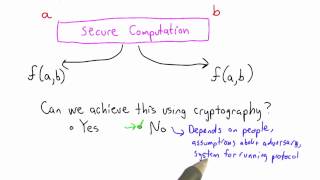
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Storing Passwords - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

OWASP AppSecUSA 2011:How NOT to Implement Cryptography for the OWASP Top 10 (Reloaded)
Speaker: Anthony J. Stieber This talk is an update of a talk in 2008 at the OWASP Minneapolis-St.Paul Chapter which was about encryption as it applies to parts of the OWASP Top Ten. The new talk uses fresh examples of application cryptography successes and failures, and also incorporates
From playlist OWASP AppSecUSA 2011

DEFCON 19: We're (The Government) Here To Help: A Look At How FIPS 140 Helps (And Hurts) Security
Speaker: Joey Maresca Many standards, especially those provided by the government, are often viewed as more trouble the actual help. The goal of this talk is to shed a new light onto onesuch standard (FIPS 140) and show what it is inteded for and how is can sometimes help ensure good desi
From playlist DEFCON 19

Secure computation with RAMs - Dr Mariana Raykova, Yale University
Secure computation with RAMs: revisiting square root ORAM and low leakage secure Boolean queries Hiding memory access patterns is required for secure computation, but remains prohibitively expensive for many interesting applications. This talk presents two works addressing this question:
From playlist Turing Seminars

Master Secret - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Free CISSP Training Videos | CISSP Tutorial Online Part 3
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CISSP-4u04FcVYD2c&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp
From playlist CISSP Training Videos [2022 Updated]

CERIAS Security: Protocols and Systems for Privacy Preserving Protection of Digital Identity 4/5
Clip 4/5 Speaker: Abhilasha Bhargav-Spantzel In this presentation I introduce a number of techniques that address the above problems. The approach is based on the concept of privacy preserving multi-factor identity verification. The main technique consists of verifying multiple identifie
From playlist The CERIAS Security Seminars 2007

Compromising the Tesla Model X Keyless Entry
This talk covers a practical security evaluation of the Tesla Model X keyless entry system. We will cover the internal workings of the system, including the key fob, the body control module and the pairing protocol. Additionally, we detail our reverse engineering techniques and document se
From playlist Security

Thanks to the DeepSec organisation for making these videos available and let me share the videos on YouTube. Speaker: Karsten Nohl This is the GSM security follow-up to DeepSec 2007. Karsten Nohl explains the state of GSM security by adressing the weaknesses of GSM A5 encryption. For m
From playlist DeepSec 2009

Stanford Seminar - Intel Software Guard Extensions
"Intel Software Guard Extensions: Innovative Instructions for Next Generation Isolated Execution"- Frank Mckeen of Intel Colloquium on Computer Systems Seminar Series (EE380) presents the current research in design, implementation, analysis, and use of computer systems. Topics range from
From playlist Engineering

RSA Conference 2010 USA: The Cryptographers Panel 4/6
Clip 4/6 MODERATOR: Ari Juels, Chief Scientist and Director, RSA Laboratories PANELISTS: Whitfield Diffie, Martin Hellman, Ronald Rivest, Adi Shamir, Brian Snow Join the founders of the field for an engaging discussion about the latest advances in cryptography, research areas to wa
From playlist RSA Conference USA 2010

Private Messages Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
