
Convincing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Primality (1 of 2: Fermat's Test)
From playlist Cryptography
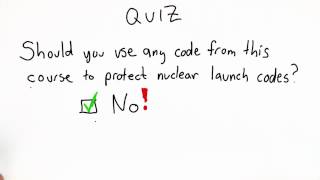
Do Not Implement Your Own Crypto Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Symmetric Cryptosystems - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
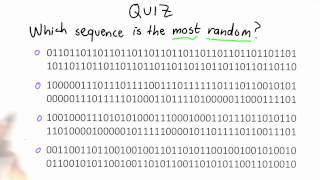
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Congratulations - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

HAR 2009: How we eavesdropped 100% of a quantum cryptographic key 6/6
Clip 6/6 Speakers: Ilja Gerhardt, Vadim Makarov Quantum cryptography, as being based on the laws of physics, was claimed to be much more secure than all classical cryptography schemes. (Un)fortunately physical hardware is not beyond of an evil control: We present a successful attack of
From playlist Hacking at Random (HAR) 2009

Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
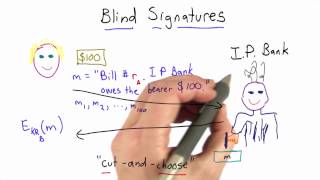
Blindfolded Signatures - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cut and Choose - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Frequency stability property short film | Computer Science | Khan Academy
Courses on Khan Academy are always 100% free. Start practicing—and saving your progress—now: https://www.khanacademy.org/computing/computer-science/cryptography/crypt/v/frequency-stability Can you tell the difference between actions based upon flipping a coin and those based upon blind g
From playlist Journey into cryptography | Computer Science | Khan Academy

Stanford Webinar - Cryptocurrencies and Blockchains: The Science Behind the Technology, Dan Boneh
Professor Dan Boneh discusses the science of blockchains, decentralized applications, and where the technology is headed. Learn more: https://online.stanford.edu/courses/xcs251-cryptocurrencies-and-blockchain-technologies #cryptocurrency #blockchain
From playlist Stanford Webinars
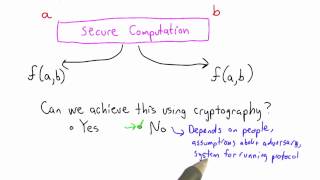
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Anne Broadbent - Information-Theoretic Quantum Cryptography Part 2 of 2 - IPAM at UCLA
Recorded 27 July 2022. Anne Broadbent of the University of Ottawa presents "Information-Theoretic Quantum Cryptography" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: These lectures are an introduction to the interplay between quantum information and cryp
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Blind Signatures Protocol - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

RSA Blind Signatures - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Blind Signatures Protocol Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
