
Computer Basics: What Is a Computer?
Computers are all around us, and they play an important role in our lives. But what exactly is a computer? We're going to answer that question and give you an overview of some of the different types of computers you might use. 0:00 Intro 0:22 Ones and zeros 0:39 Hardware and software 1:0
From playlist Starting out with Technology

How to get 64 bit installations for your 64-bit Python modules
Having installation problems? Import problems? Live to fight another day with: http://www.lfd.uci.edu/~gohlke/pythonlibs/ No more crying when you can't find a 64-bit python installer for your favorite module!
From playlist Big Data Analytics & Algorithmic Stock Trading / Backtesting

An introduction to the 16-byte by 8-bit static RAM that we're going to build for our 8-bit computer. Support me on Patreon: https://www.patreon.com/beneater Previously we built a 1-bit register: https://youtu.be/-arYx_oVIj8 Next we extended that to build an 8-bit register: https://youtu
From playlist Building an 8-bit breadboard computer!

Mathsplanations: 64-Bit is Mathematically Better
In this video we discuss just how much more data a 64 bit system can handle compared to a 32 bit system... and if you guessed double, you're in for a surprise Another useful dose of Maths for everyone by Dr Sarada Herke. For more in-depth videos check out my Graph Theory channel http://y
From playlist Mathsplanations

Bitwise Operators 2: The OR Operation
This computer science video describes the bitwise operation OR. It explains how the OR operation works with unsigned integers and how the OR operation can be used with a bitmask to manipulate the contents of a register containing bit flags. The equivalent OR operators are demonstrated i
From playlist Bitwise Operators

What Is Quantum Computing | Quantum Computing Explained | Quantum Computer | #Shorts | Simplilearn
🔥Explore Our Free Courses With Completion Certificate by SkillUp: https://www.simplilearn.com/skillup-free-online-courses?utm_campaign=QuantumComputingShorts&utm_medium=ShortsDescription&utm_source=youtube Quantum computing is a branch of computing that focuses on developing computer tech
From playlist #Shorts | #Simplilearn

How Does a Quantum Computer Work?
For more on spin, check out: http://youtu.be/v1_-LsQLwkA This video was supported by TechNYou: http://bit.ly/19bBX5G A quantum computer works in a totally different way from a classical computer. Quantum bits or 'qubits' can exist in a superposition state of both zero and one simultaneousl
From playlist From Transistors to Quantum Computers
How we represent numbers in computers. Part of a larger series teaching programming. Visit codeschool.org Twitter: @brianwill
From playlist Numbers as bits

Training Image & Text Classification Models Faster with TPUs | by Lak Lakshmanan | Kaggle Days SF
Lak Lakshmanan "Training image and text classification models faster with TPUs" Kaggle Days San Francisco held in April 2019 gathered over 300 participants to meet, learn and code with Kaggle Grandmasters, and compete in our traditional offline competition. This edition is presented by
From playlist Kaggle Days San Francisco Edition | by LogicAI + Kaggle
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Block Cipher Standards (AES) (Contd.)
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
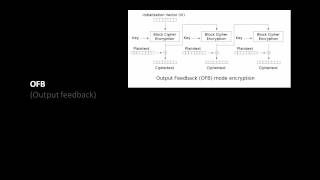
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Lecture 7: Side Effects - Richard Buckland UNSW 2008
The Adversary and adversary models of computation: an all powerful force out to get you. Side Effects: in machine code, in c functions, in general. Returning a value from main. Also: ASCII, talking in lectures, mars bars and Marco Polo and the emperor of china. Music: Triohatala
From playlist CS1: Higher Computing - Richard Buckland UNSW

Message Authentication Codes and HMAC
From playlist Cryptography Lectures

AES and DES Algorithm Explained | Difference between AES and DES | Network Security | Simplilearn
In today's video on AES and DES algorithm explained, we cover a major aspect of network security in encryption standards.The origins and working of both the data encryption standard and advanced encryption standard are covered. We also look into the applications and differences between AES
From playlist Cyber Security Playlist [2023 Updated]🔥

AES - Advanced Encryption Standard Algorithm In Cryptography | AES Explained | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=AES-Z_7aOkS8tOA&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?u
From playlist Big Data Hadoop Tutorial Videos For Beginners [2022 Updated]

Discrete Structures: Hashing and Password Cracking
A review of hashing algorithms, including MD5. Hash collisions. Plus: cracking passwords!
From playlist Discrete Structures


