
Secret Sharing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
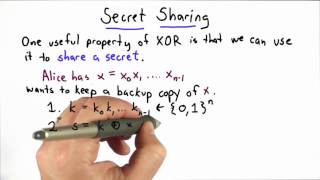
Secret Sharing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Hashing And EKE - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

SSH Authentication Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Trusted Third Party Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Storing Passwords Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Voter Identity Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Importance Of Keys Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain

ShmooCon 2013: Crypto: You're Doing It Wrong
For more information and to download the video visit: http://bit.ly/shmoocon2013 Playlist ShmooCon 2013: http://bit.ly/Shmoo13 Speaker: Ron Bowes As a group. the security industry has solved a lot of difficult problems. Firewalls do a great job blocking traffic, overflow vulnerabilities
From playlist ShmooCon 2013

Mathematics in Cryptography III - Toni Bluher
2018 Program for Women and Mathematics Topic: Mathematics in Cryptography III Speaker: Toni Bluher Affiliation: National Security Agency Date: May 24, 2018 For more videos, please visit http://video.ias.edu
From playlist Mathematics

Discovering Hidden Properties to Attack NodeJS Ecosystem
Node.js is widely used for developing both server-side and desktop applications. It provides a cross-platform execution environment for JavaScript programs. Due to the increasing popularity, the security of Node.js is critical to web servers and desktop clients. We present a novel attack
From playlist Security

Messenger Hacking: Remotely Compromising an iPhone through iMessage
So called “0-click” exploits, in which no user interaction is required to compromise a mobile device, have become a highly interesting topic for security researchers, and not just because Apple announced a one million dollar bug bounty for such exploits against the iPhone this year. This t
From playlist Security

Anne Broadbent - Information-Theoretic Quantum Cryptography Part 1 of 2 - IPAM at UCLA
Recorded 27 July 2022. Anne Broadbent of the University of Ottawa presents "Information-Theoretic Quantum Cryptography" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: These lectures are an introduction to the interplay between quantum information and cryp
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

SOURCE Boston 2008: Keynote - Dan Geer
Speaker: Daniel Earl Geer Jr., Sc.D For more information visit: http://bit.ly/SOURCE_Boston_2008_information To download the video visit: http://bit.ly/SOURCE_Boston_2008_videos
From playlist SOURCE Boston 2008
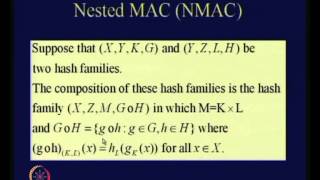
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cyber Security Full Course 2023 | Cyber Security Course Training For Beginners 2023 | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CyberSecurityFullCourse2023-hXSFdwIOfnE&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.
From playlist Cyber Security Playlist [2023 Updated]🔥

DeepSec 2007: Doppelgänger - novel protection against unknown file format vulnerabilities
Thanks to the DeepSec organisation for making these videos available and let me share the videos on YouTube. Speaker: Rich Smith, Hewlett-Packard Labs, Trusted Systems Lab The presentation intends to discuss the development of a general technique for protection against unknown threats t
From playlist DeepSec 2007

Picking E And D Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Ethical Hacking Full Course | Ethical Hacker Course For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EHFCourseNov16-VL5261WGa70&utm_medium=DescriptionFF&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp?utm_ca
From playlist Simplilearn Live