
Improve your Linux Security and Lock User Accounts After Failed Login Attempts
Linux Security is always important and more so on public systems. Using PAM to lock user accounts after a number of failures will greatly help prevent scripted attacks against your PAM protected Linux systems. We look at the pam_tally2 module on Ubuntu 20.04 and correct ordering of entrie
From playlist Learning Ubuntu Server

Modules in Python | What is Module | Python Tutorial for Beginners | Edureka
( Python Training : https://www.edureka.co/python ) Modules in Python are simply Python files with the .py extension, which implement a set of functions. Modules are imported from other modules using the import command.A module allows you to logically organize your Python code. Grouping r
From playlist Python Tutorial For Beginners | Edureka

Cool Python Modules | Modules In Python | Useful Python Modules | #Shorts | Simplilearn
🔥Enroll for Free Python Course & Get Your Completion Certificate: https://www.simplilearn.com/learn-python-basics-free-course-skillup?utm_campaign=CoolPythonModulesShorts&utm_medium=ShortsDescription&utm_source=youtube Python is a beginner-friendly language. With an easy syntax and tons o
From playlist #Shorts | #Simplilearn

Python 3 Programming Tutorial - urllib module
The urllib module in Python 3 allows you access websites via your program. This opens up as many doors for your programs as the internet opens up for you. urllib in Python 3 is slightly different than urllib2 in Python 2, but they are mostly the same. Through urllib, you can access website
From playlist Python 3 Basics Tutorial Series
Commutative algebra 39 (Stably free modules)
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We discuss the relation between stably free and free modules. We first give an example of a stably free module that is not fre
From playlist Commutative algebra
Commutative algebra 41 Locally free modules
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We define locally free modules and explain that they are analogs of vector bundles in geometry. We give some examples of local
From playlist Commutative algebra

Commutative algebra 40 The Eilenberg Mazur swindle
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We describe the Eilenberg-Mazur swindle, a technique making using of "paradoxical" properties of infinite sets. As examples we
From playlist Commutative algebra

Commutative algebra 38 Survey of module properties
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We give a short survey of some of the properties of modules, in particular free, stably free, Zariski locally free, projectiv
From playlist Commutative algebra

Commutative algebra 44 Flat modules
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We summarize some of the properties of flat modules. In particular we show that for finitely presented modules over local ring
From playlist Commutative algebra

Limit login attempts with pam_tally2 in Ubuntu
Limiting user login attempts when an incorrect password is used is an absolute must in securing your system against cybersecurity attacks. If password login is allowed then we can limit the attempts before an account is locked. We use Ubuntu 18.04 and pam_tally2.so Additionally you can fin
From playlist Learning Linux Security and LPIC-3 303
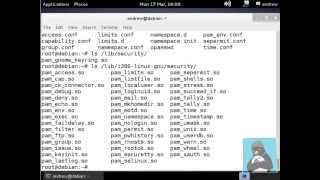
More videos like this online at http://www.theurbanpenguin.com In this video we look at configuring PAM, Plugable Authentication Modules doe the LPIC-2 level 2 certification and the 202 exam. We will see how we can disable logins, restrict multiple logins and disable access to ssh etc
From playlist LPIC-2

Commutative algebra 42 Projective modules
This lecture is part of an online course on commutative algebra, following the book "Commutative algebra with a view toward algebraic geometry" by David Eisenbud. We discuss the relation between locally free things (vector bundles) and projective things. In commutative algebra and differe
From playlist Commutative algebra

Linux Essentials For Hackers - #17 - SSH And SSH Security
Welcome to the Linux Essentials For Hackers series, where we will be covering the 20% you need to know to be efficient with Linux. In this video, we will take a look at how to setup OpenSSH and SSH key-based authentication. This series is sponsored by Linode, use the link below to get 20
From playlist Linux Essentials For Hackers

Linux Essentials For Hackers - #15 - TOR & Proxychains
Welcome to the Linux Essentials For Hackers series, where we will be covering the 20% you need to know to be efficient with Linux. In this video, we will take a look at how to use TOR in conjunction with proxychains for anonymity. This series is sponsored by Linode, use the link below to
From playlist Linux Essentials For Hackers

Alexander Dranishnikov (9/22/22): On the LS-category of group homomorphisms
In 50s Eilenberg and Ganea proved that the Lusternik-Schnirelmann category of a discrete group Γ equals its cohomological dimension, cat(Γ) = cd(Γ). We discuss a possibility of the similar equality cat(φ) = cd(φ) for group homomorphisms φ : Γ → Λ. We prove this equality for some classes of
From playlist Topological Complexity Seminar

Itertools in Python - Advanced Python 07 - Programming Tutorial
Itertools in Python - Advanced Python 07 - Programming Tutorial In this Python Advanced Tutorial, we will be learning about the itertools module in Python. The itertools module is a collection of tools for handling iterators. It offers some advanced tools like product(), permutations(), c
From playlist Advanced Python - Complete Course

Andy Magid, University of Oklahoma
Andy Magid, University of Oklahoma Differential Brauer Monoids
From playlist Online Workshop in Memory of Ray Hoobler - April 30, 2020

Andy Magid, University of Oklahoma (hybrid talk)
October 21, Andy Magid, University of Oklahoma Differential Projective Modules
From playlist Fall 2022 Online Kolchin seminar in Differential Algebra

Embedded Recipes 2018 - WooKey: the USB Battlefront Warrior - Mathieu Renard, Ryad Benadjila
USB devices are nowadays ubiquitous and participate to a wide variety of use cases. Recent studies have exposed vulnerabilities on the USB implementations, and among them the BadUSB attacks are a serious threat against the integrity of USB devices. Firmwares, hosts Operating Systems, as we
From playlist Embedded Recipes 2018
