Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security

Signature Validation - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
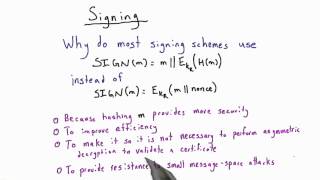
Signing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Certificates And Signatures Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DEFCON 13: On the Current State of Remote Active OS Fingerprinting
Speaker: Ofir Arkin, CTO and Co-Founder, Insightix Active operating system fingerprinting is a technology, which uses stimulus (sends packets) in order to provoke a reaction from network elements. The implementations of active scanning will monitor the network for a response to be, or no
From playlist DEFCON 13
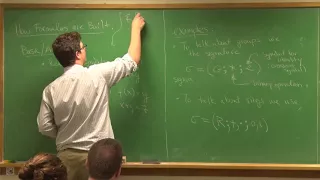
Fundamentals of Mathematics - Lecture 14: Signatures, Formulas, Structures, Theories, and Models
course page: http://www.uvm.edu/~tdupuy/logic/Math52-Fall2017.html videography - Eric Melton handouts - DZB, Emory
From playlist Fundamentals of Mathematics

Advanced Bitcoin Scripting -- Part 1: Transactions & Multisig
This is the first part of a more technical talk where Andreas explores Bitcoin script, with examples from the 2nd edition of Mastering Bitcoin, focusing on the use of conditional statements, flow control, guard clauses and time locks. The examples will include advanced multi-signature scri
From playlist Bitcoin Talks by Andreas M. Antonopoulos

Hermann Schulz-Baldes: Computational K-theory via the spectral localizer.
Talk by Hermann Schulz-Baldes in Global Noncommutative Geometry Seminar (Europe) http://www.noncommutativegeometry.nl/ncgseminar/ on March 24, 2021
From playlist Global Noncommutative Geometry Seminar (Europe)

MIT MAS.S62 Cryptocurrency Engineering and Design, Spring 2018 Instructor: Tadge Dryja View the complete course: https://ocw.mit.edu/MAS-S62S18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP61KHzhg3JIJdK08JLSlcLId Discussion of hash signatures, public and private keys
From playlist MIT MAS.S62 Cryptocurrency Engineering and Design, Spring 2018

DEFCON 13: DIRA: Automatic Detection, Identification, and Repair of Control-Hijacking Attacks
Speakers: Alexey Smirnov, Student, SUNY Stony Brook Tzi-cker Chiueh, Professor, SUNY, Stony Brook Buffer overflow attacks are known to be the most common type of attacks that allow attackers to hijack a remote system by sending a specially crafted packet to a vulnerable network applicat
From playlist DEFCON 13

Syntax and Semantics - Benedikt Ahrens
Benedikt Ahrens Universite Nice Sophia Antipolis; Member, School of Mathematics September 25, 2012 For more videos, visit http://video.ias.edu
From playlist Mathematics

OHM2013: SIM card exploitation
For more information visit: http://bit.ly/OHM13_web To download the video visit: http://bit.ly/OHM13_down Playlist OHM 2013: http://bit.ly/OHM13_pl Speaker: Karsten Nohl SIM cards are among the most widely-deployed computing platforms with over 7 billion cards in active use, but little i
From playlist OHM 2013

Sandipan Kundu - 1/2 Causality in Conformal Field Theory
https://indico.math.cnrs.fr/event/3308/ Causality places nontrivial constraints on QFT in Lorentzian signature, for example fixing the signs of certain terms in the low energy Lagrangian. In these pedagogical lectures, I will explore causality constraints on conformal field theory. First,
From playlist Sandipan Kundu - Three Lectures on Causality in Conformal Field Theory

27c3: Die gesamte Technik ist sicher (de)
Speakers: Dominik Oepen, Frank Morgner Possession and knowledge: Relay attacks on the new ID card For the new electronic identity card three different readers classes are specified, the simplest of which has already undergone some criticism. After the discussion about the security of the
From playlist 27C3: We come in peace

Can't edit signature in Outlook fix
Has your signature button disappeared in outlook? Tried to go into options to edit the signature but the buttons are all greyed out? This is how you fix it.
From playlist Technology